Telegram channels used to doxx and report Hong Kong protesters to Chinese authorities
Channels are collecting and submitting personally identifiable information of Hong Kong protesters to China’s Ministry of StateSecurity
Telegram channels used to doxx and report Hong Kong protesters to Chinese authorities

BANNER: (Source: @KaranKanishk via Wikimedia Commons)
A pro-China Telegram channel is identifying Hong Kong’s pro-democracy protesters and rioters with an aim to build a database of them and submitting their information to China’s Ministry of State Security Reporting Platform.
In an environment where anonymity is possible and often desirable, exposing sufficient information to identify a person — or even the threat of it — is a frequent tactic to silence or intimidate the person being exposed. This phenomenon of exposing otherwise anonymous people’s personally identifiable information (PII), “doxxing,” is a darker manifestation of open-source research.
Once a person has been doxxed, they often experience a significant amount of online and, frequently, real-life harassment. Combining the tactic with a referral to a national government — especially one with a reputation for mass surveillance and societal control — for punitive action is an elevation in anti-democratic behavior.
Doxxing is becoming a potent weapon for both sides — pro-democracy and pro-China — of the ongoing protests in Hong Kong.
Doxxing on public channels
One of the primary Telegram channels through which protesters are doxxed is 好孩子特輯(逃犯條例 (“Good Kids [Fugitive Offenders Ordinance]”) or, alternatively, “Yeeseelostandfound” as it labelled itself in English. When the DFRLab started its analysis, the channel’s name was “父母搵仔女(逃犯條例)” (“Parents and children [Fugitive Offenders Ordinance]”) and updated its name during the course of the analysis.
The administrator for the channel, in particular, appears to play a primary role in its activities. They either crowdsource the work by posting a photo and asking for help in identifying the person or people in the photo, which they request to receive privately (i.e., not in channel). Or they simply post an after-submission notice, putting forth the PII and a photo for somebody they say has been submitted to the Chinese government.

The channel also posts information about pro-democracy participants whose pictures have been lifted from private — usually pro-democracy — channels or that have been posted as a part of media reports.
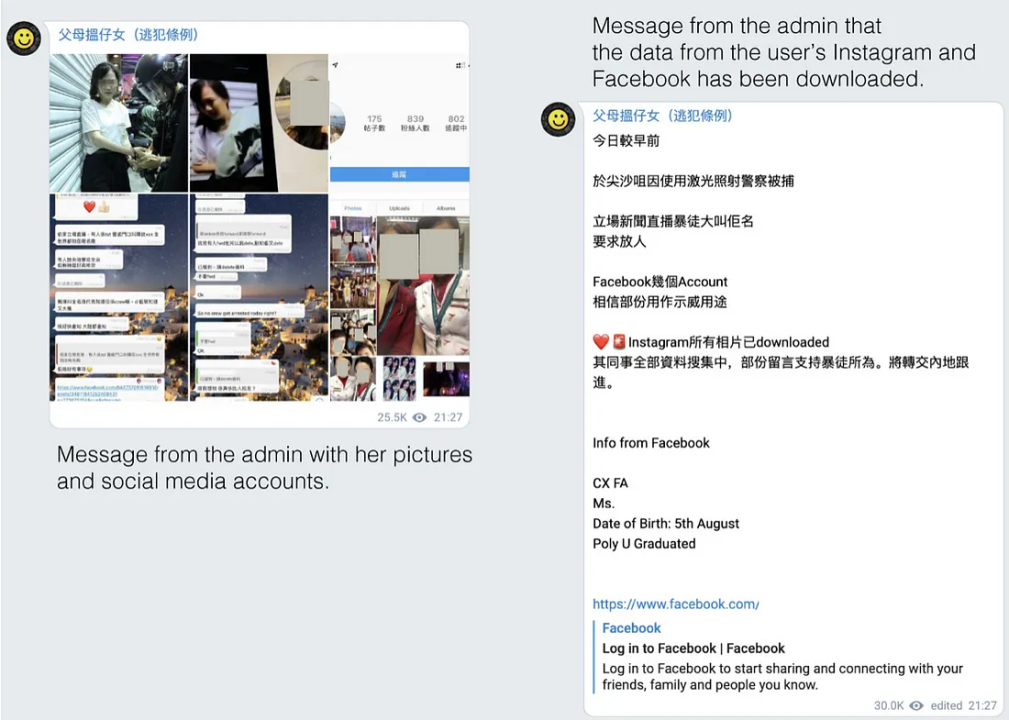
The channel also claimed that it scrapes PII of people from social platforms such as Instagram and Facebook.

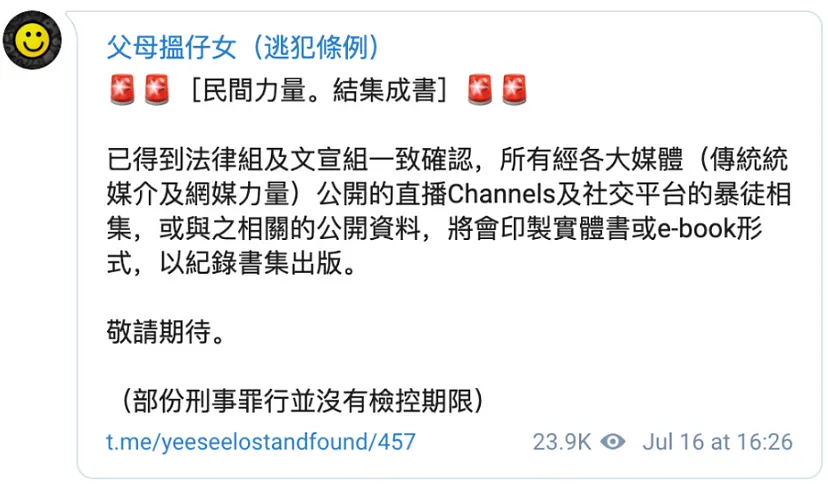
As stated in one of the messages, the channel claims that it is building an e-book or a physical book of personal information of protesters.
But this is not the only channel that keeps an eye on protesters, as the DFRLab discovered another channel that doxxes protesters and labels them as “cockroaches.” People who oppose the pro-democracy protests have adopted the term to refer to protesters.

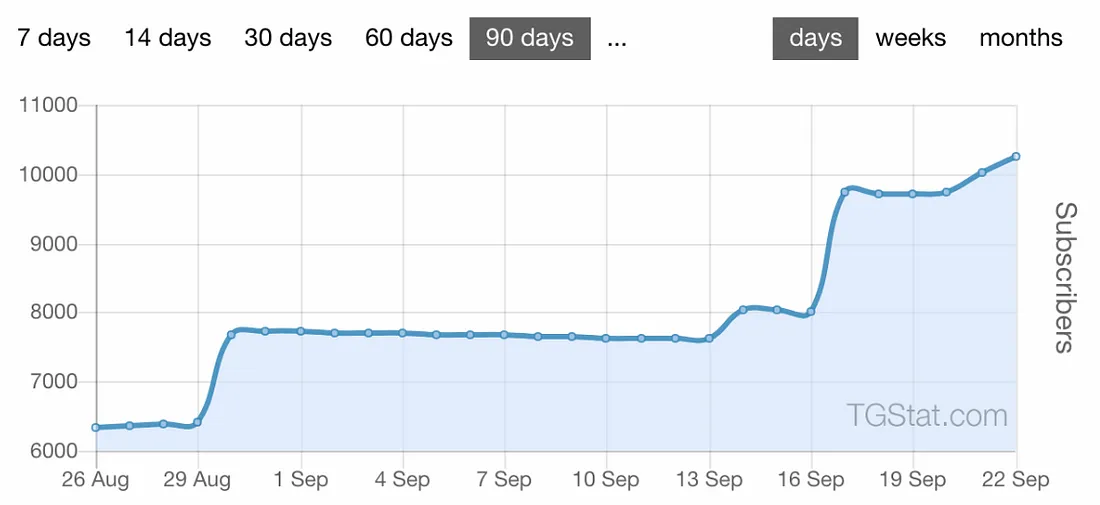
This Telegram channel slowly growing and has gained a few thousand followers in the past few days, even though the channel activity has subsided over the past few days.
Users have reported these channels to Telegram and expressed their frustrations regarding the doxing attempts by pro-China channels.
Reporting information to China
As claimed by the channel, the members of the channel are expected to share personal information of protesters and report it on China’s Ministry of State Security Reporting Platform.
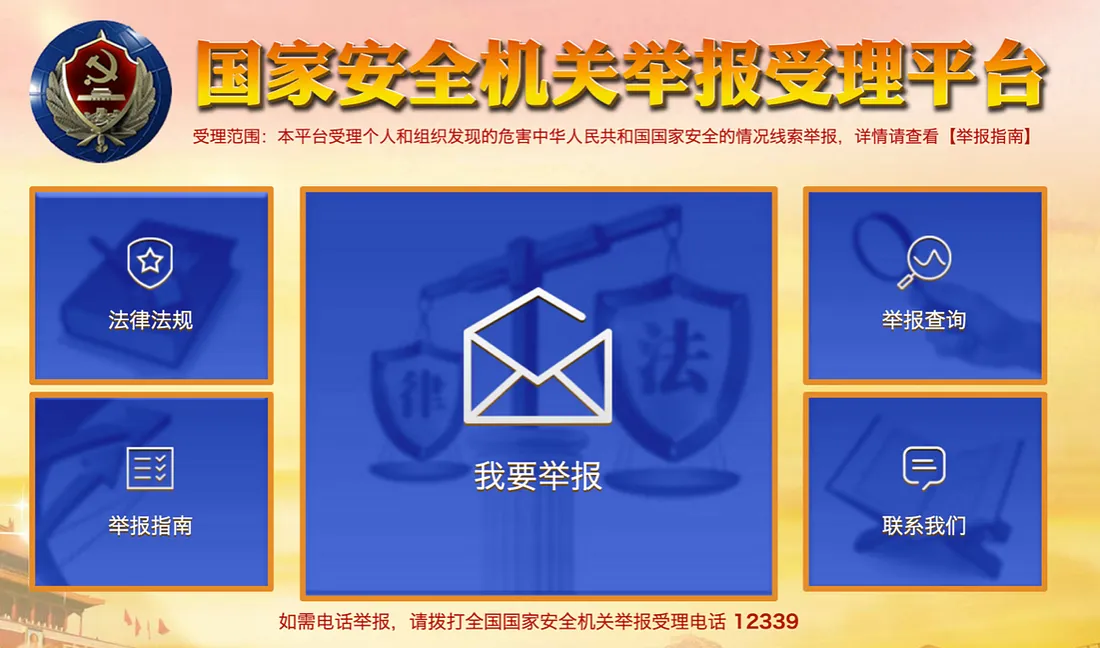
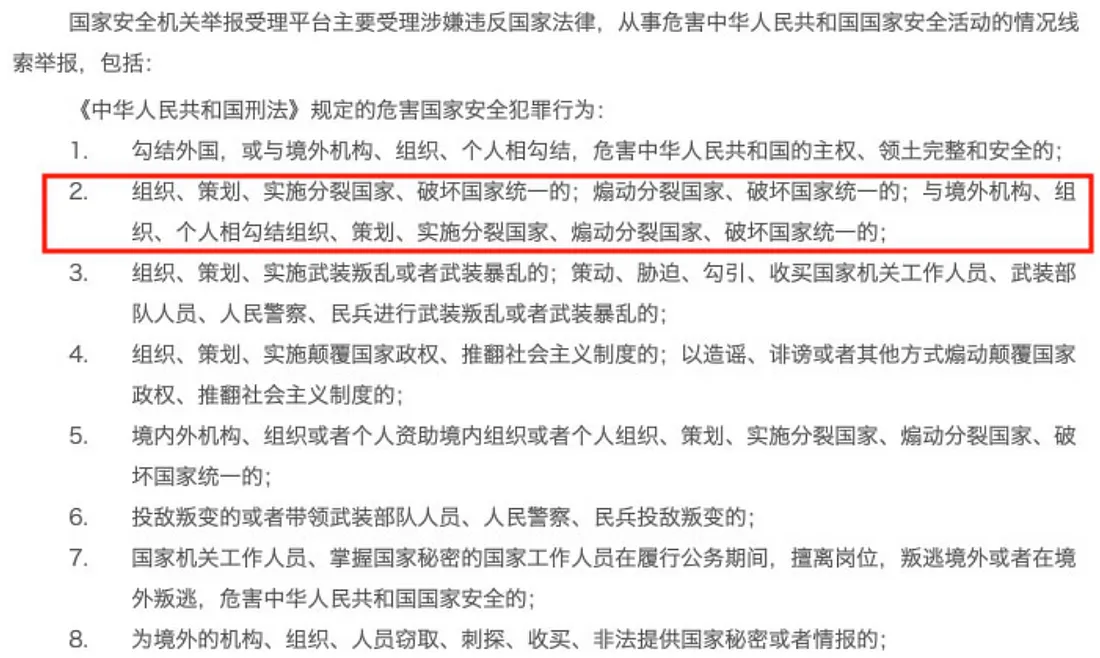
The website, 12339.gov.cn, is a platform for reporting crimes of national security, including espionage, and for submitting other clues on “national security behaviors.” The website claims to keep the source of the information confidential. While reporting an incident on the website, a list appears in pop-up form with instructions on what should be reported, some of which could be interpreted to include even peaceful demonstrations.
In particular, the second criterium in the list states that a person can be submitted for intent to “[o]rganize, plan, or implement the secession of the country and undermine national unity; provoke to disunite the country and undermine the state unity; in collusion with institutions, organizations, or individuals outside the territory to organize, plan, or implement the secession of the country and undermining national unity, to provoke to disunite the country and to undermine the state unity.”
The same rhetoric of gathering information on protesters for China’s national security reporting portal was found on several Facebook pages.

Channels broadcasting information on the Hong Kong police
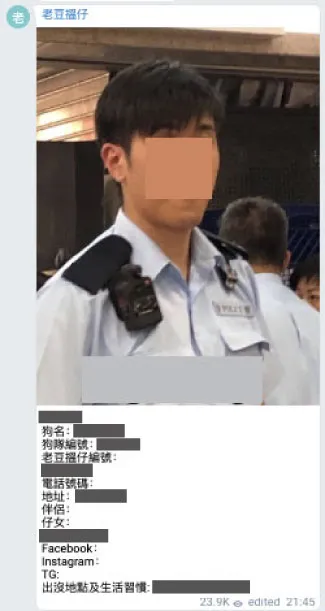
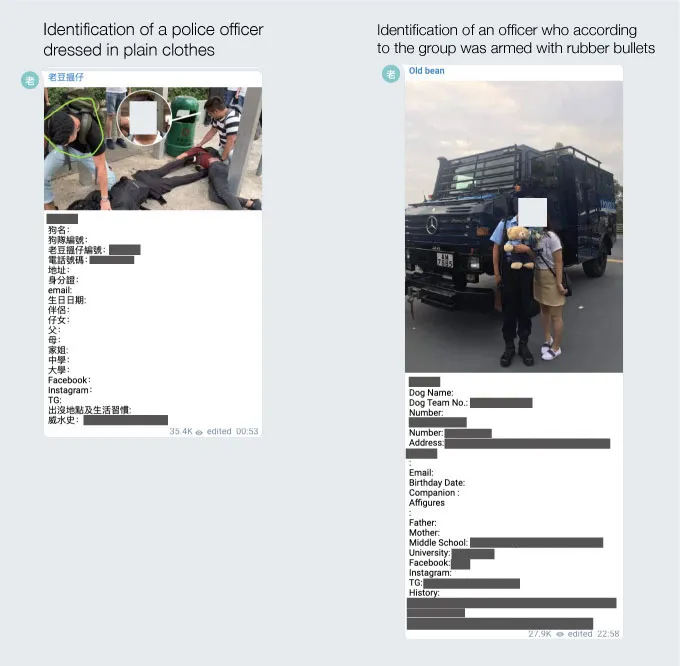
Meanwhile, a counterpart Telegram channel called DadFindboy is doxxing police officers who acted against the protesters. The channel seems to implement more sophisticated doxxing than pro-Chinese ones, as the amount of information compiled by this channel is highly detailed, including family relations such as a father or mother’s name.
Conclusion
The Hong Kong protests have revealed how Telegram channels could become a significant doxing mechanism. Telegram channels are preferred as they safeguard the privacy of individuals in the channel while they simultaneously carry out these malicious attacks. There have been attempts to report channels like these, but the channels remain active and continue to report information to their subscribers, and to the Chinese authorities.
As of now, it is not clear what the outcomes may be from the information passed to the mainland, but it sets out an important discussion that Chinese national security and the government’s online reporting platform is being misused for forwarding information of Hong Kong nationals who support the pro-democratic movement.
Though there are efforts on both sides of the political spectrum — pro-China and pro-democracy — to doxx protest participants and police officers, respectively, the pro-democracy demonstrators are under greater threat. The balance of power between the Telegram channels greatly favors those that are pro-China, as the outcome of their efforts could potentially lead to intervention by the Chinese state in enforcing punitive actions. This last threat is felt particularly acutely by the protesters, as the protests originally arose because the Hong Kong government put forward a bill that would have allowed for extradition to mainland China of anybody arrested in the territory.
Follow along on Twitter for more in-depth analysis from our #DigitalSherlocks.

