Suspicious accounts spread COVID-19 disinfo in Armenian Facebook groups
Amid tensions with Azerbaijan, Facebook accounts
Suspicious accounts spread COVID-19 disinfo in Armenian Facebook groups

Amid tensions with Azerbaijan, Facebook accounts spread false claim about an Armenian military unit and coronavirus
Suspicious accounts — some of them likely hacked or inauthentic — spread disinformation in several Armenian Facebook groups on March 30–31 2020, alleging that COVID-19 had spread through an Armenian military unit stationed in Noyemberyan, a town in Armenia’s northeast Tavush Province bordering Azerbaijan.
Armenia has not been immune from the infodemic that has gripped much of the world as the coronavirus pandemic spreads. Conspiracies regarding the pandemic have abounded in Kremlin-sponsored outlets, as well as in fringe and domestic sources. On March 20, the country’s National Security Service announced that it had discovered that “hackers, some of them from the Republic of Azerbaijan,” had gained access to the social media accounts of Armenian Facebook users and spread disinformation about the coronavirus in Armenia from their accounts.
As of March 30, the Armenian Ministry of Defense spokesperson reported six confirmed cases of COVID-19 among servicemen. There have been no official reports of widespread infection among units in the Noyemberyan region.
Claims of an Azerbaijan connection
The offending text read as follows, translated from Armenian:
My relative serves as a driver in a military unit in Noyemberyan. He was distributing food to the soldiers in the trenches. Two days ago, medical workers visiting the military unit transported him and 13 of his fellow servicemembers, with whom he had contact, to the hospital. Doctors say he was infected with coronavirus in a military unit stationed in the city and then passed it on to his fellow soldiers in the trenches. What is my relative’s fault? If there had been no virus in the food warehouse in the city, he would not have been infected or transmitted it to members in his unit. His family is also quarantined.
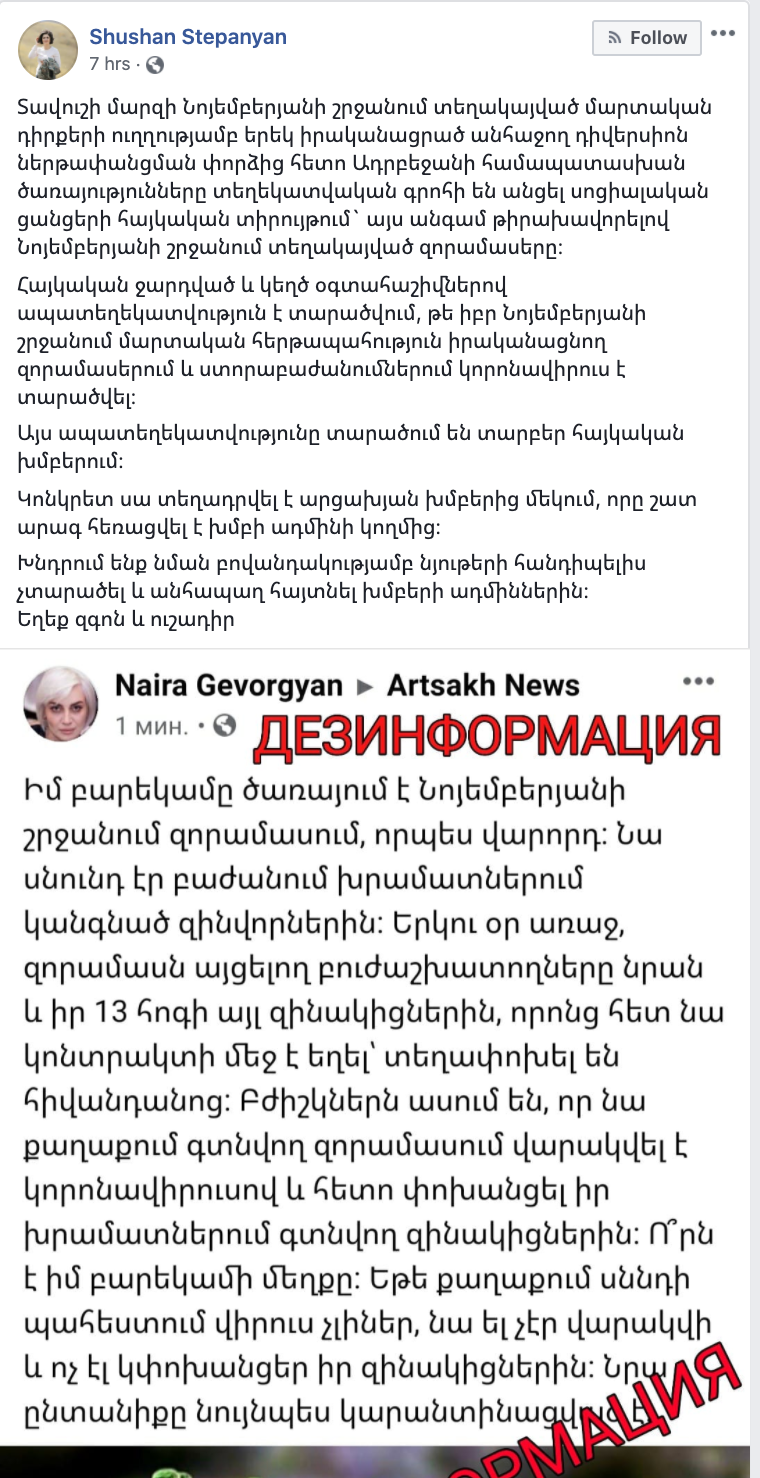
Armenia’s Ministry of Defense spokesperson, Shushan Stepanyan, wrote on her personal Facebook profile that the posts amounted to an “information offensive” by Azerbaijani security services. This attribution carries particular weight in light of an escalation between the two countries just 24 hours prior, when a child was reportedly wounded in a shelling attack from the Azerbaijani side in the Noyemberyan area.
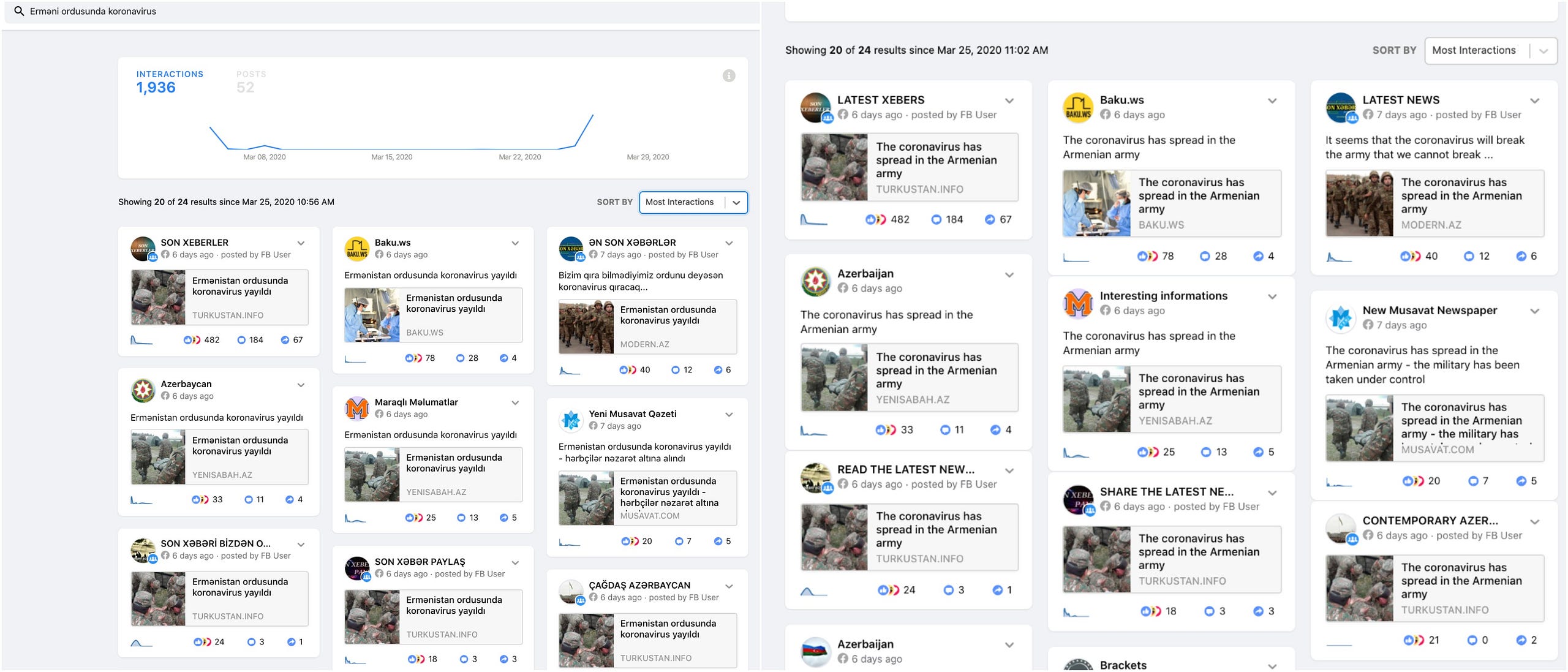
In a previous case involving an inauthentic Facebook persona spreading disinformation in Armenia, the disinformation was quickly picked up and disseminated by Azerbaijani media outlets. In this case, the DFRLab did not find evidence that Azerbaijani media picked up this particular post; but a CrowdTangle search of the Azerbaijani words Erməni ordusunda koronavirus (“Armenia military coronavirus” according to Google Translate) revealed that over the past week Azerbaijani outlets have been heavily — and increasingly — covering reports of COVID-19 infection in the Armenian military, sometimes resorting to hyperbole.
Copypasta from suspicious accounts
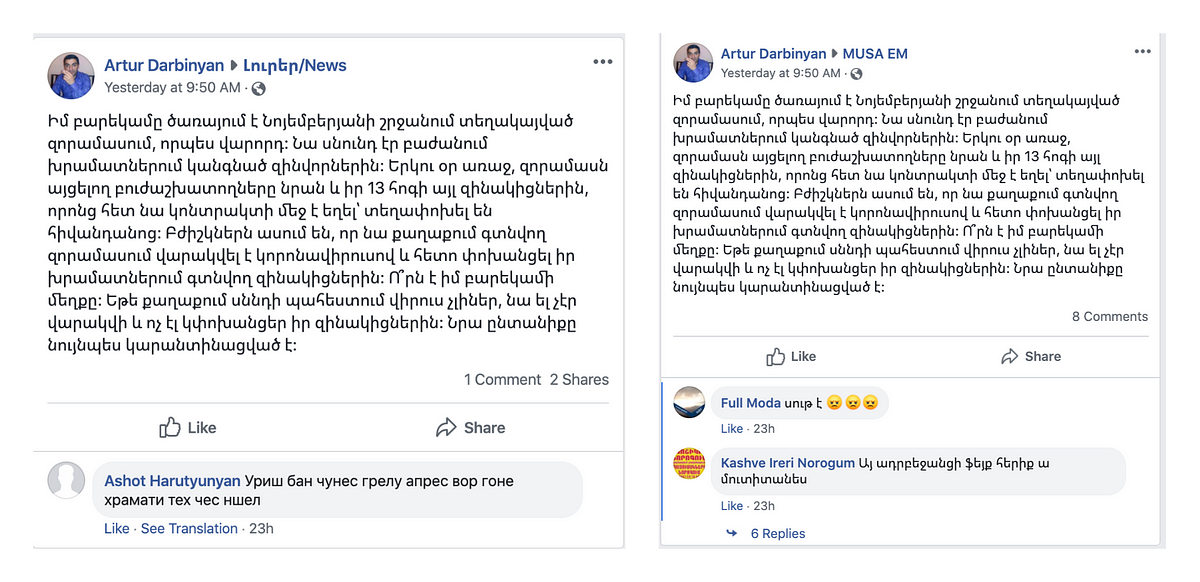
A search via social media listening tool CrowdTangle surfaced four instances of the verbatim text on Facebook, all from ostensibly Armenian users writing in Armenian. Two of the posts had already been removed from Facebook by the time of writing, but they remained preserved in the CrowdTangle database.
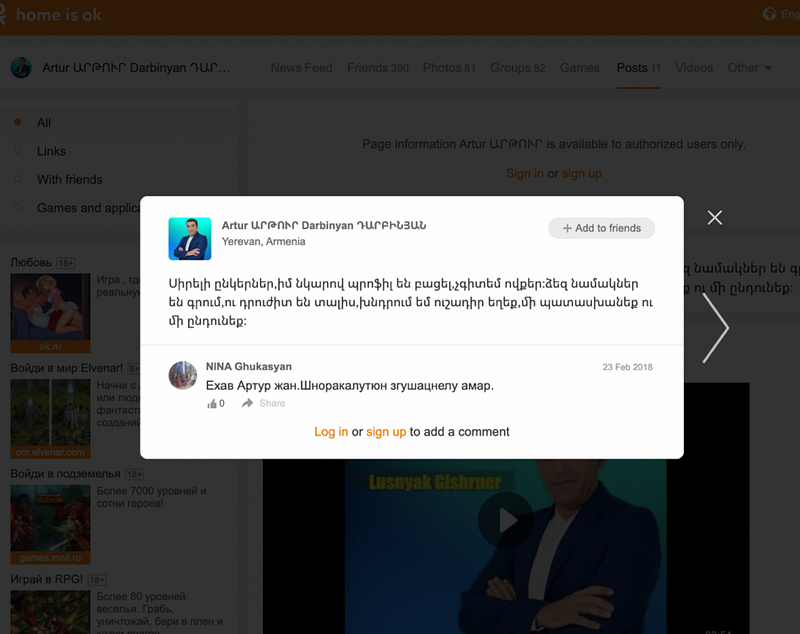
The first appearance of the text was posted at 9:50 a.m. on March 30 by a user named Artur Darbinyan in two popular Armenian Facebook groups, each with tens of thousands of members.
The DFRLab found that a user by the same name — Artur Darbinyan — and with the same previous profile picture posted a status in early 2018 on his profile on the Russian social networking site Odnoklassniki, warning his connections that someone had created a profile using his photo and was sending messages to them as well as friend requests. This indicated that as early as 2018, someone may have been using Darbinyan’s identity to operate inauthentic profiles on social media.
A third post appears to have been removed, but was still visible in CrowdTangle as appearing in a Karabakh-focused news group on March 31, at 1:46 a.m. Two minutes later, the duplicate text appeared in a group for Armenian Prime Minister Nikol Pashinyan’s supporters. This time, the post included a meme of the Ministry of Defense spokesperson, Shushan Stepanyan, with a speech bubble that read “Pashinyan is not a man.”

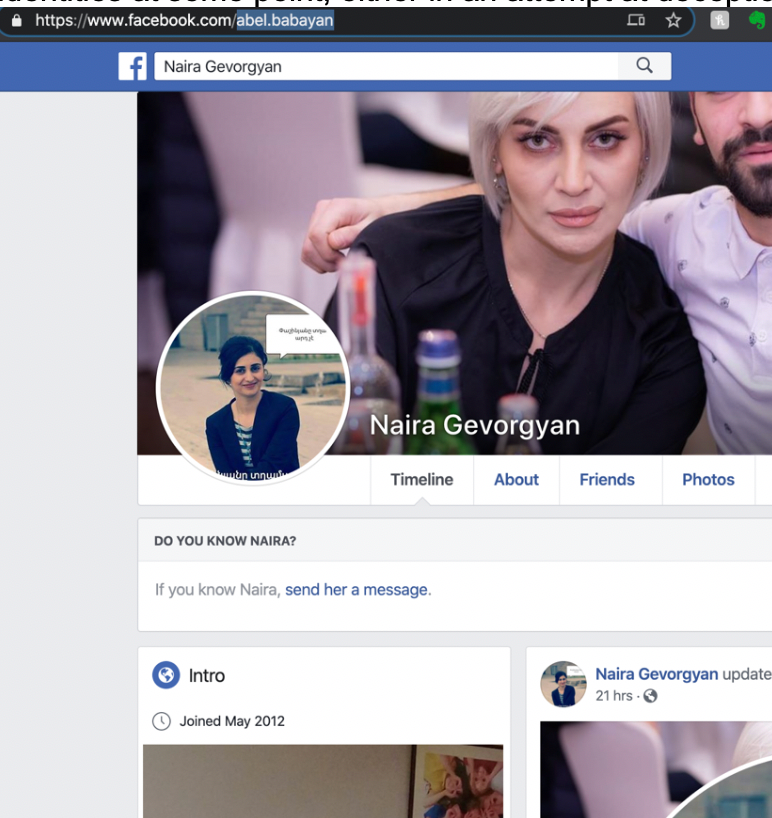
The user who shared the above posts, captured in screenshots by various Armenian FB users, had the display name “Naira Gevorgyan.”
The DFRLab found this profile but noticed that her display name and her vanity Facebook URL ID did not match one another. While the profile’s display name was “Naira Gevorgyan,” its Facebook URL ID indicated a man’s name: abel.babayan. This discrepancy suggested that the account may have changed identities at some point, either in an attempt at deception on the owner’s part or because it had been hacked.
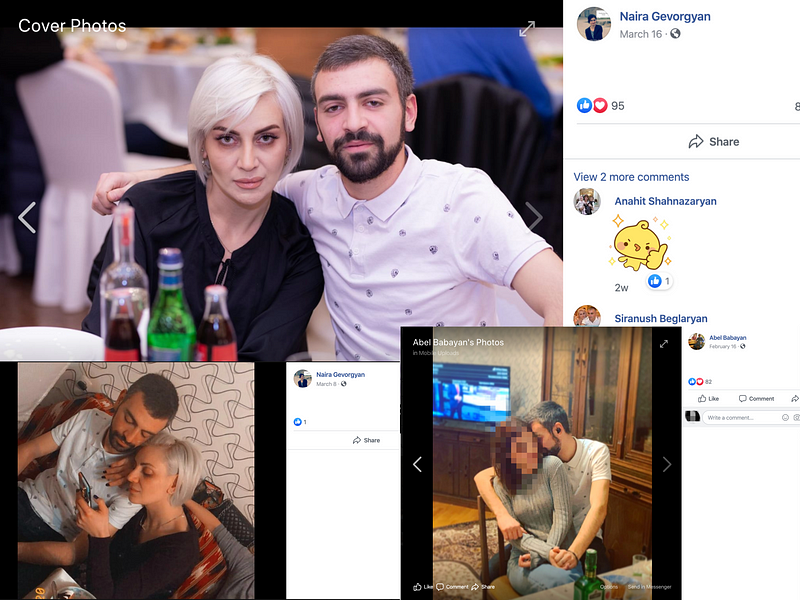
The DFRLab came across a profile for a presumably real “Abel Babayan” — and was able to link his profile to the “Naira Gevorgyan” profile via his public friends list.
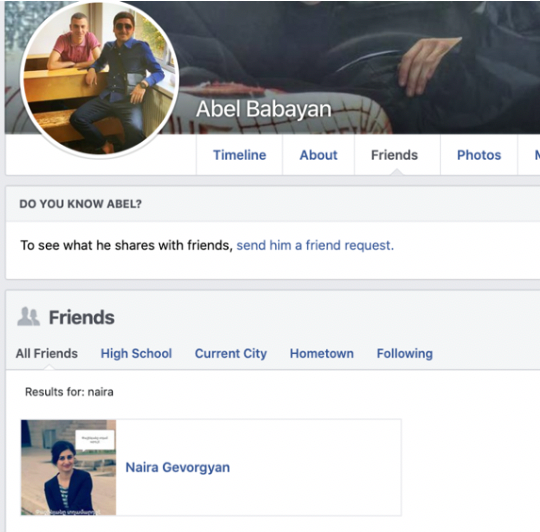
In addition, on both Abel and “Naira’s” profiles, Abel appeared wearing the same shirt.
While it is unusual that “Naira” claimed a vanity URL in Babayan’s name and the two appeared together in pictures on their respective profiles, there was no additional open-source evidence to suggest that Babayan’s profile was somehow involved in spreading the disinformation on Armenian Facebook groups: he has no suspicious post history. It is possible that his original account, the one with the abel.babayan vanity URL, was hacked and the display name changed. This would not explain, however, why Abel would send a friend request to or accept one from a hacked profile. The DFRLab has reached out to Babayan for comment but has not received a response.
Reports of a hacked Facebook page run from Azerbaijan
The only open-source evidence linking this instance of disinformation to someone in Azerbaijan was the Facebook fan page of Armenian singer Armen Movsisyan. The page also posted the identical text, which Movsisyan later disavowed on his personal page, writing that hackers had taken control of his fan page and posted disinformation from his name.
Movsisyan’s fan page has since been removed from Facebook, but a Page Transparency section screenshot the DFRLab obtained several hours prior to its removal identified a single page manager, located in Azerbaijan.
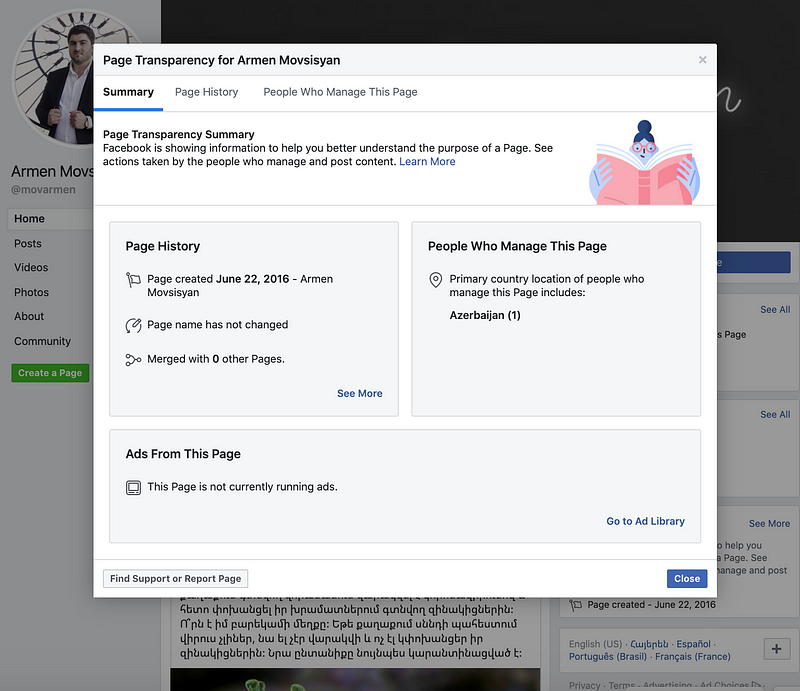
This is consistent with the reporting of Armenian fact-checking initiative Infocheck.am, which in March 2019 reported that the page may have been hacked from Azerbaijan and had published false information about Armenian military casualties related to the Karabakh conflict.
In both the case of Armen Movsisyan’s Facebook fan page and the profile of Artur Darbinyan, there is a record of allegations stretching back at least a year from other accounts in their name — which appear to be run by the real Movsisyan and Darbinyan — accusing other profiles of impersonation.
This instance of disinformation comes as Armenia, a country of just under three million, struggles with the most confirmed cases of COVID-19 in the South Caucasus, as Armenia-Azerbaijan tensions reach a flashpoint after a recent military incident, and as voters headed to the polls in the breakaway region of Nagorno-Karabakh, the heart of the Armenian-Azerbaijani conflict.
While the open-source evidence cannot attribute this case to a particular source, it does lay one thing bare: the actors responsible chose a moment primed for disinformation on this topic to thrive. Just as Armenians’ anxiety over COVID-19 was mounting online, fatigue over both the overabundance and questionable quality of information on the outbreak was setting in, and a longstanding territorial and ethnic conflict risked bubbling over further.
Zarine Kharazian is Assistant Editor with the Digital Forensic Research Lab.
Follow along on Twitter for more in-depth analysis from our #DigitalSherlocks.

