Putin’s Email Scandal Continues
Ukrainian Hackers Leak Key Kremlin Aide’s Email… Again
Putin’s Email Scandal Continues
Share this story
Today, Ukrainian hackers released a second cache of emails tied to Vladislav Surkov, a key Kremlin figure overseeing the Minsk ceasefire agreement and, as many have contended, an architect of Russia’s strategy to take Crimea and supervise pro-Russian separatists in eastern Ukraine. The first release, which DFRLab analyzed last week, exposed specific details regarding Surkov’s cooperation with Donetsk separatist leaders, most notably Denis Pushilin. However, more often, the first leak of emails showed us Surkov’s concern with the media environment of Ukraine and the perceptions in Russia, Ukraine, and the West regarding figures and projects related to the self-declared republics of the Donbas. Analysis of the second leaked inbox, with emails ranging from November 2014 to September 2016, shows many of the same concerns in these emails, along with new revelations.
Comparison between leaks
Like with the first leaked inbox, the second batch of Surkov emails was published by a Ukrainian hacker group — this time by “Kiberalyans” (Cyber Alliance), which includes “CyberHunta,” the publisher of the first inbox. While the first inbox contained .PST files — data files for Microsoft Outlook inboxes — the second inbox are .MBOX files — common for web mail inboxes, such as Gmail. This difference is consistent with the source of the two inboxes: the first (PST) is from Surkov’s “incoming” (приемная) inbox on a Russian government server (prm_surkova@gov.ru), which presumably used Outlook. The second (MBOX) is another “incoming” inbox for Surkov that was hosted on the popular web client Mail.ru (pochta_mg@mail.ru). These inboxes are not Surkov’s personal inbox, but something closer to “The Desk of Vladislav Surkov,” in the context of an American or British business. In both inboxes, there are superfluous emails that match their respective hosts: the first inbox had routine messages from Russian government IT employees, while the second inbox is filled with spam from Mail.ru advertising services and mentioning holidays.
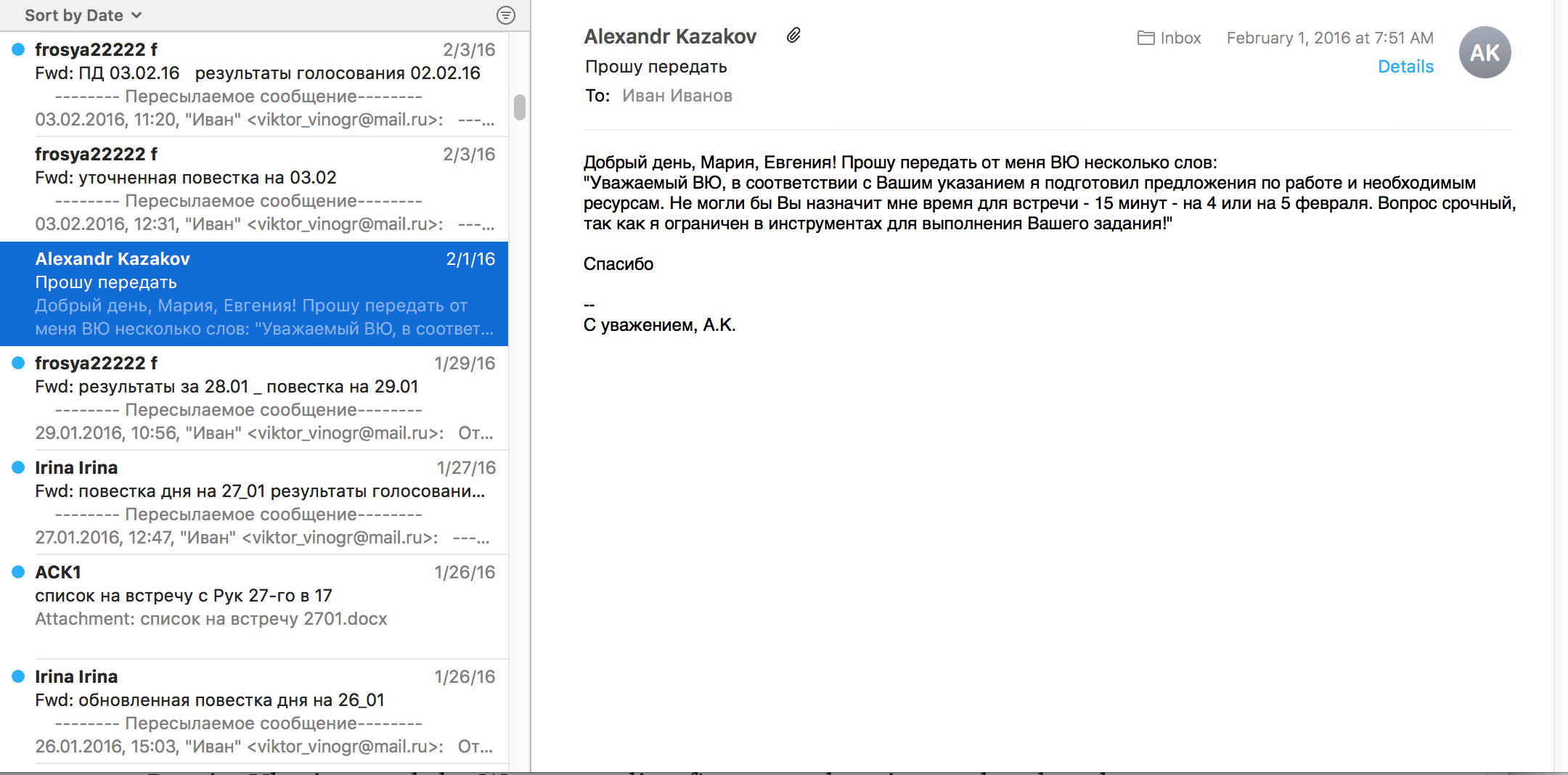
The operators of two leaked inboxes are also the same: two Surkov assistants named Maria and Yevgenia. There are numerous opportunities where we can verify this information, ranging from addressees mentioning the name of Maria or Yevgenia (for example, in an April 6, 2015 email, the sender says “Thanks Maria,” or on November 13, when the sender says “Good day, Yevgenia!”) or an order confirmation to Maria for a shipment at a Moscow store. There are no indications that Surkov himself personally uses the email, and we often see messages passed second-hand from Maria or Yevgenia to recipients. For example, in a June 2015 email, the operator of the inbox replies to an email with the message “The answer of V.Yu: Thank you for the information…” (V.Yu. refers to Vladislav Yuryevich, the first name and patronymic of Surkov).
In both leaked inboxes, the bulk of the messages are daily or weekly reports on topics curated by Surkov. While the first leaked inbox included hundreds of reports on Abkhazia and South Ossetia, most of the reports in the second inbox are related to Ukraine, especially regarding the progress of potential laws under consideration in the Ukrainian Verkhovna Rada (parliament).
A typical document can be seen below, which was sent from “ACK1” (ask1@digitalsafe.com) with the subject line “Monitoring 22 September.”
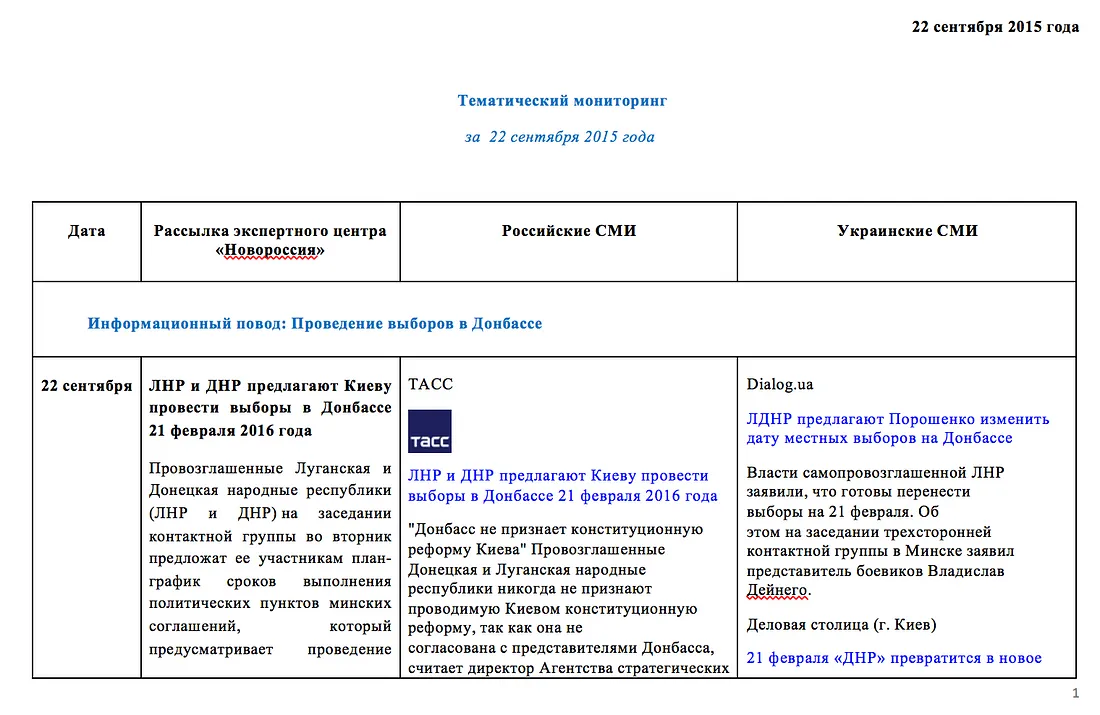
The document entitled “Thematic monitoring for 22 September 2015,” as seen in the screenshot above, includes the date of monitored materials, and three columns for Russian, Ukrainian, and “Electronic Center of ‘Novorossiya’” for the topic of elections in the Donbas. The document gives brief synopses of articles on this subject in Russian state media (TASS, RIA Novosti), independent or semi-independent Russian media (NTV, RBC), and various Ukrainian outlets (TSN, 112, Ostrov).
Authenticity
The first dump of emails was widely viewed as genuine, including from American and Ukrainian intelligence officials. In DFRLab’s analysis, all evident indications pointed towards the authenticity of the leaked materials. The email headers (metadata) appeared reliable, individual incidents could be confirmed with hard-to-find and public information, and various individuals independently confirmed that they had sent emails that appeared in the hacked materials.
The second email cache shows similar signs of authenticity. The raw headers from randomly selected leaked emails appear authentic, but verification of every email in the inbox requires significant digital forensics work. The raw header information for a routine email from the aforementioned ask1@digitalsafe.com address can be found below. This metadata shows that the message was routed through a Swiss server, which matches the Switzerland-based Digital Safe origin address.
X-Mozilla-Status: 0001
X-Mozilla-Status2: 00000000
Delivered-To: pochta_mg@mail.ru
Return-path: <ask1@digitalsafe.com>
Authentication-Results: mxs.mail.ru; spf=pass (mx30.mail.ru: domain of digitalsafe.com designates 80.80.230.40 as permitted sender) smtp.mailfrom=ask1@digitalsafe.com smtp.helo=smtp3.globexdata.ch
Received-SPF: pass (mx30.mail.ru: domain of digitalsafe.com designates 80.80.230.40 as permitted sender) client-ip=80.80.230.40; envelope-from=ask1@digitalsafe.com; helo=smtp3.globexdata.ch;
Received: from [80.80.230.40] (port=24764 helo=smtp3.globexdata.ch)
by mx30.mail.ru with esmtp (envelope-from <ask1@digitalsafe.com>)
id 1ZYxpg-0008Ld-Ol
for pochta_mg@mail.ru; Mon, 07 Sep 2015 17:55:46 +0300
X-Mru-BL: 0:0
X-Mru-BadRcptsCount: 0
X-Mru-PTR: smtp3.globexdata.ch
X-Mru-NR: 1
X-Mru-OF: Linux (Ethernet or modem)
X-Mru-RC: CH
Received: from dfr-media-backup.s3.amazonaws.com (dfr-media-backup.s3.amazonaws.com [127.0.0.1])
by smtp3.globexdata.ch (Postfix) with ESMTP id 46EDC22A2EE3
for <pochta_mg@mail.ru>; Mon, 7 Sep 2015 14:55:36 +0000 (UTC)
X-Virus-Scanned: Debian amavisd-new at blade03.securusvault.ch
Received: from smtp3.globexdata.ch ([127.0.0.1])by dfr-media-backup.s3.amazonaws.com (blade03.securusvault.ch [127.0.0.1]) (amavisd-new, port 10024)
with ESMTP id m1O1NJiKozLB for <pochta_mg@mail.ru>;
Mon, 7 Sep 2015 14:55:34 +0000 (UTC)
Received: from [192.168.1.200] (unknown [213.181.23.252])
by smtp3.globexdata.ch (Postfix) with ESMTPA id 25FAA22A0A03
for <pochta_mg@mail.ru>; Mon, 7 Sep 2015 14:55:30 +0000 (UTC)
Message-ID: <55EDA55A.2000900@digitalsafe.com>
Date: Mon, 07 Sep 2015 17:55:22 +0300
From: =?UTF-8?B?0JDQodCaMQ==?= <ask1@digitalsafe.com>
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:31.0) Gecko/20100101 Thunderbird/31.7.0
MIME-Version: 1.0
To: pochta_mg@mail.ru
Subject: =?UTF-8?B?0LzQvtC90LjRgtC+0YDQuNC90LMg0LTQu9GPINCg0YPQutC+0LLQvtC0?=
=?UTF-8?B?0LjRgtC10LvRjw==?=
Content-Type: multipart/mixed;
boundary=” — — — — — — 010902030908090702070304″
X-DMARC-Policy: no
X-Mras: Ok
X-Mru-Authenticated-Sender: ask1@digitalsafe.com
X-Spam: undefined
Like with the first inbox, we can verify events described in the emails to judge the leak’s authenticity. One of the best ways to verify leaked materials is to juxtapose information in the released emails with available open source information, along with considering the degree of difficulty to forge these materials. For example, a PDF document with no metadata attached to it that describes nefarious plans with no verifiable references should be viewed with more skepticism than receipts for airline tickets with verifiable booking codes.
An interesting example that lends credibility to the leak is an email on May 15, 2015 from Anton Malyshev, containing a draft for a screenplay called “Volunteers” written by well-known Russian filmmaker Yury Bykov. In the email, Malyshev asks the inbox operator to send along the draft to Surkov.
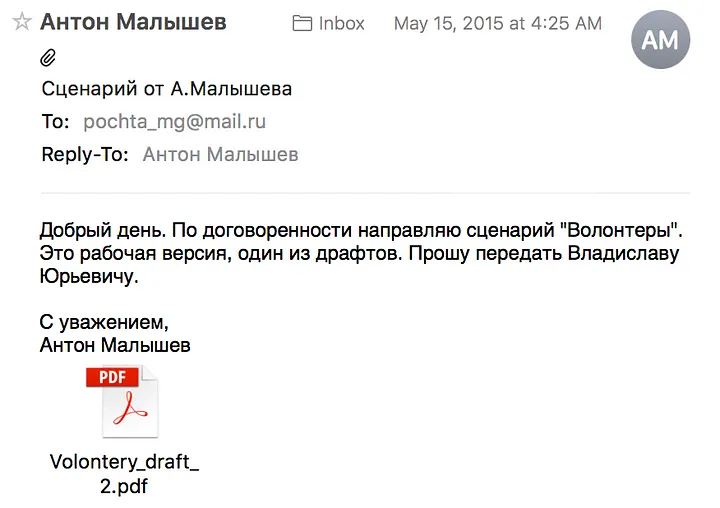
This screenplay draft is 115 pages long, and was converted to a PDF two days before the email was sent (May 13, 2015). The screenplay concerns the Ukrainian and Russians who fight in the Donbass, focusing on a Russian man named Oleg, who traveled from the Russian city of Rostov-na-Donu to Ukraine.
View the PDF here. View the original email file here (open with an email client, such as Outlook, Thunderbird, or Mac’s Mail).
The screenplay is original, and the text cannot be found anywhere online. If this screenplay is a forgery from Ukrainian intelligence services, then it was a colossal undertaking with little ideological payoff. A few days after the script was sent to Surkov, a “Bondarenko” (possibly Oleg, a common addressee in Surkov’s inbox) forwarded on his comments on the screenplay. He praises the screenplay as a potential “ideological product,” and offered other suggestions, such as a change in the title, the names of some characters, and other details. Bykov’s production of “Volunteers” was slated for a 2016 release, but has not yet been released.
Update: Today, journalists from the BBC Russian Service contacted Bykov, who confirmed his participation in the project, though did not confirm any correspondence with Surkov. Bykov has pulled out of the production of the movie after disagreements with the film studio.
There are numerous other emails that lend to the inbox’s credibility, such as a poem sent from the aide of Russian singer Iosif Kobzon months before its publication (with a few stanzas changed from the final version), but none that clearly point to signs of forgery. DFRLab cannot confirm the authenticity of every email in this leaked cache, but there were no apparent signs that any of the available materials were fabricated.
Revealing findings
Like the first leak, the second released inbox has no bombshell information that would be expected in a forged document, such as admission of culpability in the downing of MH17, receipts of payment to families of Russian soldiers who died in combat in Ukraine, and so on. Rather, as seen in the list below, the most interesting information is subtle, and in line with our previous assumptions of Surkov’s role in managing the self-proclaimed Donetsk People’s Republic.
Fomenting unrest in Kharkiv
Russian MP (in 2015) Mikhail Markelov sent a handful of documents to Surkov via his assistant, Anna Makharinskaya. In the attached documents from emails sent on April 29, June 4, and June 18, 2015, we see how Markelov proposed the creation of nominally local initiatives that were supposedly organized by Kharkov citizens. Markelov also sends Surkov lists of planned protests in Kharkov — again, supposedly with the organization and participation of local citizens. One of the locals that the then-Russian MP suggests to lead a new organization is Igor Massalov, a Ukrainian politician who organized pro-Russian demonstrations in Kharkov in 2014.
View the documents and emails sent from Markelov to Surkov here:
Future correspondence from Markelov include a list of planned events in Kharkiv, most of which were connected to the aforementioned Igor Massalov, entitled “Plan of initial measures for the election campaign in the Kharkiv Oblast,” (План мероприятий предварительного Этапа использования избирательной кампании в Харьковской области). These events were planned from “the end of June” to “the first half of August,” all before the local elections that took place in the Kharkov Oblast, among other Ukrainian regions, in October 2015. Another email from June 18 describes the organization of a flashmob protest in Kharkiv, which will “consist of 30–50 people” and where “it is necessary that people yell that Poroshenko should step down.” We encourage our readers to find possible instances of this flashmob protest taking place.
Other messages from Markelov show the clear intentions of Surkov and his proxies in Kharkiv: to foment unrest and erode the authorities of the Ukrainian government. The Russian MP and Surkov looked to create and support local pro-Russian organizations, organize events to help elect Kremli-friendly candidates, and shift public opinion towards Russia and the separatists it backs. A June 4, 2015 email from Markelov is revealing, in that he peels back the ideological-charged language that floods Russian media and shows a more pragmatic view of the situation in Kharkiv.
Warnings in the style of “Grads artillery shells are aimed at Kharkiv” and “Right Sector is planning a bloody provocation on so-and-so date” and so on are not bringing about the desired reaction.
Firstly, this is because people are tired of constant tensions and stressed out —from exhaustion and apathy. Secondly, it is because of the concentration of “intimidation” is so great that it has reached the point of absurdity.
Development of separatist propaganda
A common sight in the leaked inbox is emails from one Aleksandr Kazakov, the director of the Moscow Stolypin-Struve Center for Liberal-Conservative Policy and colleague of Russian writer Zakhar Prilepin, the author of the popular novel Sankya. Westerners know very little, if anything, about Prilepin, but he is widely respected in many circles, including the Western literary establishment (he was called “Russia’s Best Young Novelist” in Newsweek in 2011), the Russian political elite (both Putin and Medvedev have read his work), and in some anti-establishment groups (he is a member of the National Bolshevik Party). Surkov’s association with Prilepin has been long-known, as they grew up in the same city and share literary tastes. Surkov apparently worked with Surkov in the development of his book All that needs to be resolved… chronicles of an ongoing war, focusing on the Ukrainian Conflict. This book was published in the summer of 2016, after an exclusive story appeared about the text on Ukraina.ru, written by Surkov colleague Aleksandr Chalenko (who figures prominently in both the first and second email inboxes).
The book’s working title, as we discover from the leaked emails, was ‘Two Zakhars,” as it was written by Zakhar Prilepin and focused on Donetsk separatist leader Aleksandr Zakharchenko. Kazakov communicated often (sometimes, with desperation) with Surkov, hoping to gain access and arrange additional meetings between himself and Surkov.
In documents and emails sent from Kazakov, it is clear that Prilepin sought the advice of Surkov on a book on the separatist leader Aleksandr Zakharchenko, which eventually became All that needs to be resolved… In an email from February 1, 2016, Kazakov mentions an agreement made between Surkov (or “V.Yu.”)and Prilepin:
Good day, Maria and Yevgania! I ask you to pass a few words from me to V.Yu:
Dear V.Yu., in accordance with your instructions, I have prepared a proposal for work and the necessary resources. Could you please tell me a time for meeting — 15 minutes — on the 4th or 5th of February. It is an urgent question, as I am limited in regards to the tools for fulfilling your task!
Download the original email here.
While Surkov seemed to have a guiding hand and perhaps even proposed and funded the book, one should not misinterpret the cooperation to be a completely forced assignment: Prilepin has been outspoken in his support of the pro-Russian separatists in the Donbas. That said, it is not difficult to recognize the fingerprints of Surkov all over this project, as there are numerous elements of Prilepin’s book that match Surkov’s biography and past behavior.
Even more evidence of Russian arms in Ukraine
As documented by DFRLab, along with countless journalists and online investigations, a significant portion of the military equipment used in the Donbas was delivered from the Russian military. There is even more evidence of Russian involvement in the Ukrainian Conflict in January 2015 emails detailing the withdrawal of an exclusively Russian piece of military equipment.
An email from “Semyon Fish” on January 29, 2015 shows an early draft of weapon withdrawals for the eventual Minsk II ceasefire protocols. Not all of the elements in this draft made it to the final version of Minsk II, most notably the proposed withdrawal of a heavy flamethrower TOS system.
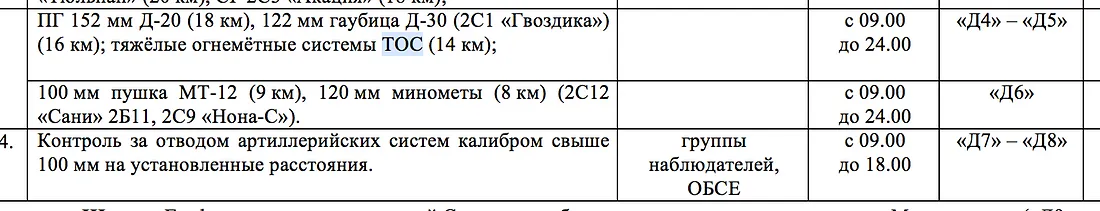
Download the original email here. Download the document concerning the withdrawal of TOS systems here.
The reason why this line is damning to Russia’s claims of non-involvement in the Ukrainian Conflict is because TOS heavy flamethrower systems are exclusively produced in Russia, and have not been exported to Ukraine. There have been OSCE reports of TOS systems sighted in Ukraine, but no confirmed uses. The inclusion of TOS systems in an early draft of the Minsk protocols is yet another piece of evidence of state-level Russian cooperation with separatist forces in eastern Ukraine.
Taken together, the two leaked Surkov inboxes shows us what we already knew: key Kremlin figures are supervising separatist officials, funding anti-government movements in Ukrainian-controlled cities, and guiding propaganda efforts related to the Ukrainian Conflict. There is little doubt that Russia will deny the importance of these leaks, but these emails provide a valuable window into the inner workings of the architect of the Crimean takeover and Ukrainian separatist movements.

