#ZapadWatch: Slavic Brotherhood combat training
Snapshots from the annual exercise between Russia, Serbia, and Belarus
#ZapadWatch: Slavic Brotherhood combat training
Share this story
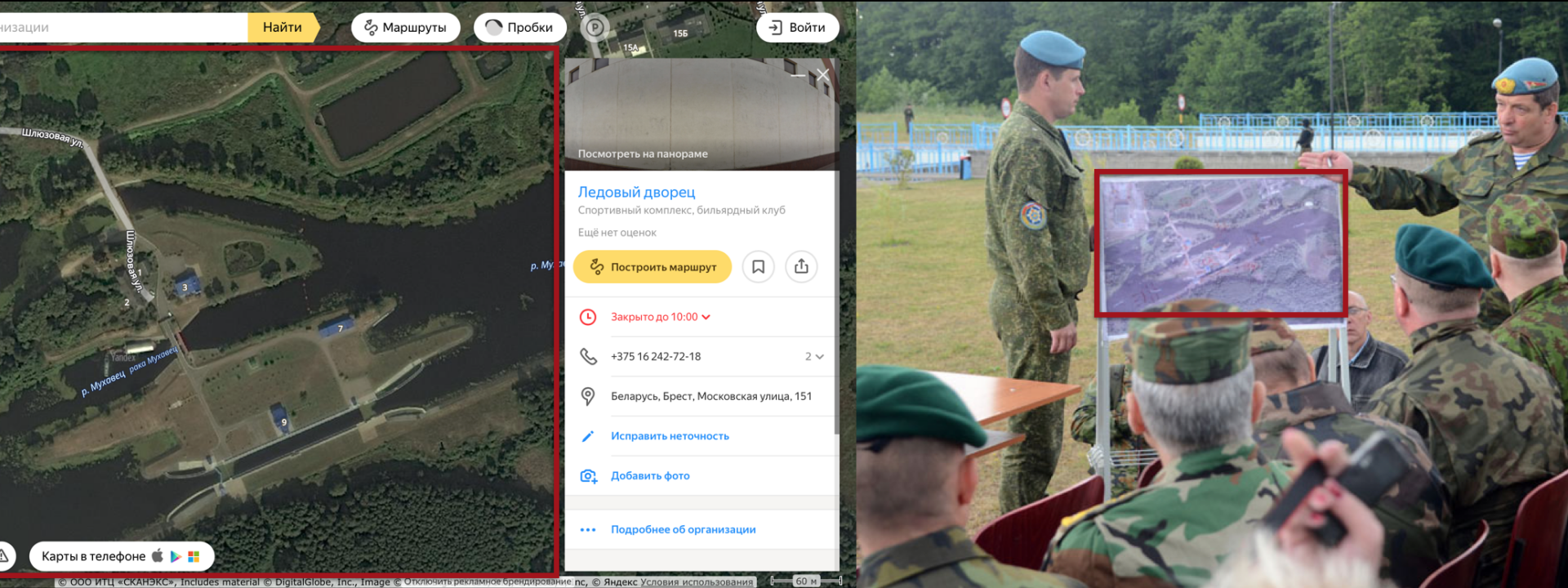
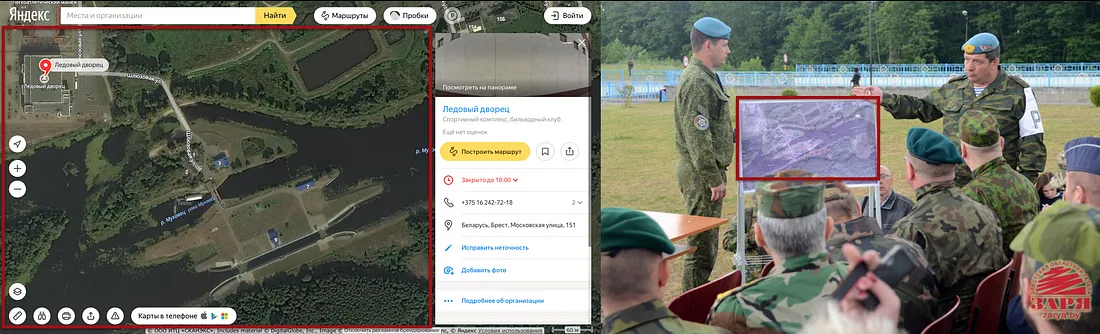
BANNER: Geolocation of the exercise, as per briefing map.
On June 6, the annual Slavic Brotherhood exercise between Russia, Belarus, and Serbia kicked off at the Brest training area in Belarus, as the @DFRLab reported. The initial phase focused on team-building; on June 12, the focus of the exercise turned to combat operations.
The Russian Ministry of Defense has provided a relatively detailed narrative of the exercise’s active second phase. According to its account, a multinational battalion tactical group, made up of paratroopers from the three countries, was tasked with reaching a designated area by crossing a water obstacle and landing from an Il-76 aircraft. Then the group had to take control over an area occupied by “terrorists.”
This involved carrying out the isolation and destruction of “illegal” armed groups, the release of “captured” infrastructure and local residents, and rendering assistance and evacuation to the “wounded” and “victims”.
On June 12, Russian Army television Zvezda TV published a story on the first day of the active phase. This showed how armored vehicles began the mission, fought a “terrorist group” attack, overcame water obstacles, and landed from the Il-76 aircraft.
A separate video released by Belarus Army TV showed the active part of the exercise, in which the “enemy” was neutralized and captured during the operation on the ground.
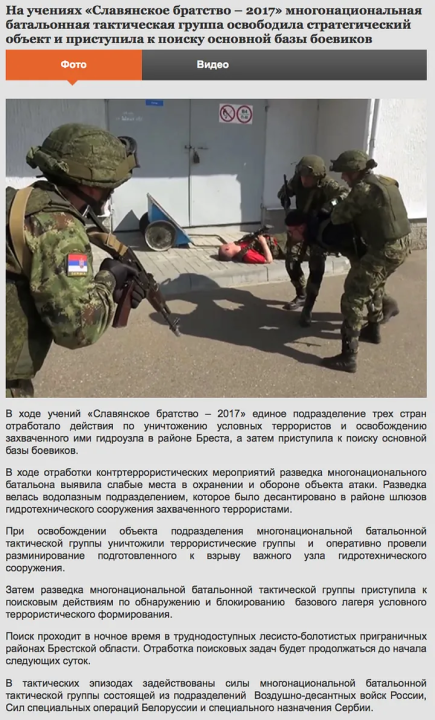
According to the Russian Ministry of Defense and Brest city’s local news portal, the multinational battle group staged the release of a captured hydro technical facility along the Mukhavets River on June 13.
On June 13, VK user Oleg Grebennikov published a post with images showing the exercise.

He wrote:
[..]Today, on one of the active phases of the exercise, the multinational battalion tactical group, formed from the units of the three member countries to carry out counter-terrorism tasks, practiced the release of the captured hydro technical facility on the Mukhavets River, the destruction of supposed terrorists and the release of hostages.
Judging from the images published by Brestcity.com, the facility where the exercise took place is located by the Ice Palace, part of the sports complex at Moskovkaya 151, Brest.


On June 13, Zvezda TV released a story showing the exercise in action.
The final stage of the active phase, as announced at the end of the report, was a parachute drop at night.
As reported by the Russian Ministry of Defense on June 14, the mission of the last exercise was to find and neutralize the headquarters of the “terrorist” group.
The article reads:
The search takes place at night in hard-to-reach wooded swampy border areas in the Brest region. The conduct of the search tasks will continue until the beginning of the next day.
The video published on June 8 by Zvezda TV showed the multinational battle group tackling tasks on ground, air, and water.
On June 9, the Russian Ministry of Defense published on its official YouTube channel footage of parachute drops by day and night.
The tasking of the troops to deal with a “terrorist” threat is consistent with the initial phase of the exercise. As the @DFRLab has noted, the scale of these operations is best viewed as a counter-insurgent operation.
The @DFRLab will continue to monitor developments around Russian military exercises, especially Zapad-2017, scheduled to be held in Belarus later this year. If you or any other #DigitalSherlocks see anything on the ground or online related to the exercises, join the conversation using #ZapadWatch.

For more in-depth analysis from our #DigitalSherlocks follow @DFRLab. This post was updated on June 16 at 1500 UTC to correct the geolocation.

