Polskanews.org: a foreign influence operation masquerading as Polish news
Linguistic, technical, and behavioral forensics uncover an influence operation against Poland bearing Russian-language fingerprints
Polskanews.org: a foreign influence operation masquerading as Polish news
Share this story
BANNER: Image generated with Claude AI, showcasing findings of the Polskanews investigations. (Source: Claude)
A joint investigation by the DFRLab and Erebus identified Polskanews.org, a Polish-language website launched in August 2020, as a likely foreign influence operation masquerading as a domestic Polish news outlet.
Understanding how we reached this conclusion requires examining the operation’s attribution signals. Attribution signals are technical traces revealing the true origins and operational characteristics of content creators, often contradicting a site’s presented identity. The most reliable signals are those that the creators cannot easily manipulate or may not realize they are leaving behind. Linguistic and infrastructural attribution signals are among the few indicators that influence operations consistently fail to eliminate.
Our forensic analysis uncovered multiple layers of such evidence. Forensic analysis of archived web content uncovered multiple attribution signals, including Russian language metadata embedded by word processing software, Cyrillic characters in file paths, phonetic and visual character substitutions consistent with Russian-speaking operators, and fabricated editorial personas using stolen photos from Russian social media. All of this evidence collectively indicates a possible foreign information operation targeting Polish public discourse and democratic institutions.
The investigation combined manual narrative analysis with automated technical forensics, progressing from contextual assessment through infrastructure mapping to deep examination of historical source code.
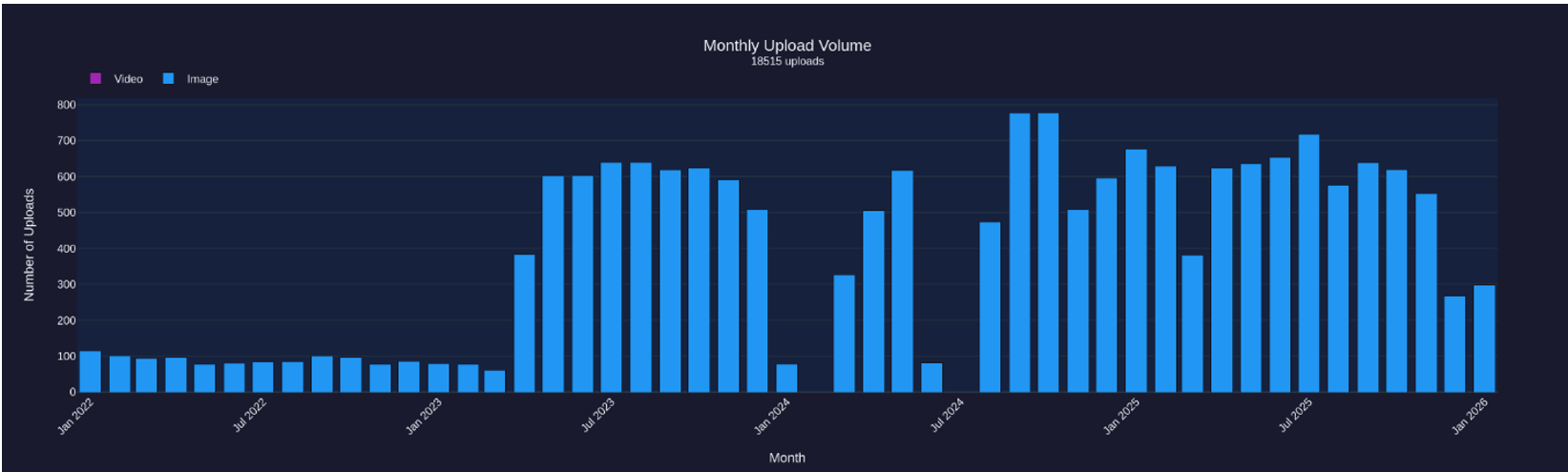
Deep forensic analysis using Erebus Forensics crawled the site’s WordPress uploads directory of 18,515 files, retrieved the complete Wayback Machine CDX index of 6,374 URLs from the Internet Archive, and downloaded 3,278 archived HTML snapshots spanning August 2020 to December 2025.
Analysis included multiple dimensions. Linguistic analysis scanned for language anomalies such as Cyrillic-range characters (U+0400–U+04FF), percent-encoded sequences, and HTML language attributes, classifying findings by type to distinguish genuine operator traces from benign third-party content. Temporal analysis extracted publication timestamps and generated activity heatmaps, revealing operational patterns including work schedules and automation deployment. Lastly, operator identification extracted WordPress artifacts such as Yoast SEO schema IDs and reversed Gravatar MD5 hashes to recover associated email addresses.
Signs of inauthenticity
Polskanews.org launched in August 2020 with a mission statement claiming to be “a free social media platform, free from all state and government organizations” aimed at providing “the latest news from Poland and the world.” Four days before the launch date, anti-government protests had erupted in Belarus, leading the Polish government to harshly criticize the Belarusian government for its massive crackdown on protesters. Polskanews.org’s contacts page lists its editorial team and others purportedly associated with the organization. Despite all team members having Polish names, the DFRLab determined that at least one persona (Marek Kołodziejczyk) is completely fabricated, and others on the website also show signs of illegitimacy. In addition, the DFRLab could not find an online presence for Polskanews.org’s managing editor, such as professional profiles, bylines in other publications, or legitimate social media accounts. In contrast, legitimate journalists typically have discoverable digital footprints.
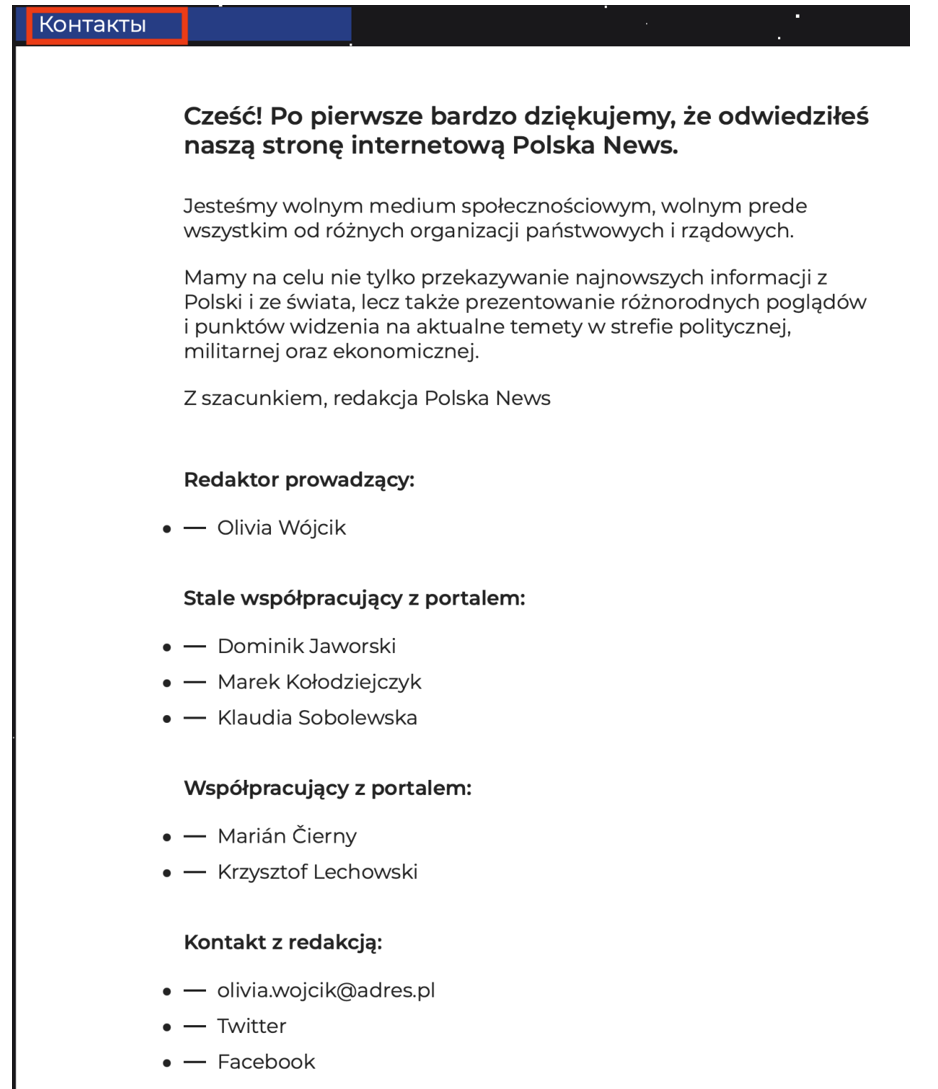
The contact section also includes a link to the outlet’s X (formerly Twitter) account, but it links to the X account of “Marek Kołodziejczyk,” who Polskanews.org claims is a regular contributor. A reverse image search of Kołodziejczyk’s profile photo revealed it was stolen from the account of a user on the Russian social media network VKontakte (VK). The DFRLab reviewed the VK profile, as well as an associated Instagram account, and concluded that he is a real individual whose VK profile picture was misappropriated by the X account, which horizontally flipped the original profile picture. Horizontal image-flipping is a common technique used to evade reverse-image searches, as search algorithms can be less effective at matching mirrored images.
The fact that the operators took this precaution suggests an awareness of digital forensic techniques. This suggests the Marek Kołodziejczyk persona is fabricated, and its associated X account is fake, representing another layer of deception in the operation’s attempt to appear authentically Polish.
Polskanews also has a Facebook page, but at the time of writing, the page was unavailable.
On the Polskanews website, articles in its “Military” and “Opinion” sections are quite often original opinion pieces unique to Polskanews rather than republished content from other media, suggesting dedicated content creation. One of the first articles published in the military section, “Why [Alyaksandr] Lukashenka does not trust Poles,” accused Poland of orchestrating Belarus’s post-election protests. The article claimed this was facilitated through a Polish American aid program, Polish cultural organizations, and NEXTA Telegram channels, which the article accused of being linked to Polish intelligence and Poland’s “Black Spiders” psychological operations unit. An Opinion section article also published in August 2020 claimed that Poland’s “interference in the affairs of another country [Belarus] can be fatal for Poland,” and that it would lead to a split within the Polish government. Another article drew false equivalence between Poland and Belarus, portraying Belarusian President Alyaksandr Lukashenka as attempting democratic reforms while claiming Poland under the Law and Justice Party (PiS) had descended into authoritarianism through judicial control and media restrictions. These articles exemplify the site’s narrative strategy: undermining Polish democracy and security measures while whitewashing authoritarian actions by Belarus. These Polskanews articles appeared during the immediate aftermath of Belarus’s contested presidential election, in parallel to Lukashenka’s accusing Poland of interfering in the country’s internal affairs. The timing suggests the site was amplifying his propaganda talking points in near-real time.
Two days before the Polish parliamentary elections in 2023, Polskanews.org published an unverified story claiming that PiS, which was in power at the time, had collected participant data from the opposition’s pro-democracy “Million Hearts march” and sent it to prosecutors, alleging that PiS was collecting a “black list” of dissidents. The article also contained a letter allegedly prepared by local authorities and a screenshot purportedly showing the collected data. No other Polish media outlet reported this story, and the DFRLab found no corroborating evidence, suggesting the letter may have been forged. Notably, while the story failed to circulate in the Polish information sphere, the Belarusian Telegram channels Yellow Plums Premium and Shvarka News amplified the article in Russian and accused Poland of draconian actions. The exclusive amplification by Belarusian channels suggests the article’s intended audience could have been Belarus itself rather than Poland.
The site’s editorial strategy shifted dramatically after Poland’s October 2023 parliamentary elections. Just four days after the elections on October 15 of that year, Polskanews.org stopped publishing original content in its “Military” and “Opinion” sections. These sections had published content since 2020 and contained the site’s most hostile anti-Polish government commentary. Following the elections, the site shifted to mostly republishing content from legitimate Polish outlets, maintaining the appearance of activity while ceasing original publishing. This timing suggests the site may have been explicitly focused on conducting an operation to influence the electoral outcome.
All of these indicators—the creation of the website amidhBelarusian protests, repetition of narratives on Poland’s interference in Belarusian affairs, the exclusive amplification of false story about Polish elections by Belarusian Telegram channels, the operational shutdown of two important sections immediately following Polish 2023 elections, and the technical attribution signals pointing to Russian-language operators—collectively suggest that Polskanews.org performed acts of information warfare targeting Poland, with the possibility of this activity being conducted by Belarusian actors.
Understanding attribution signals
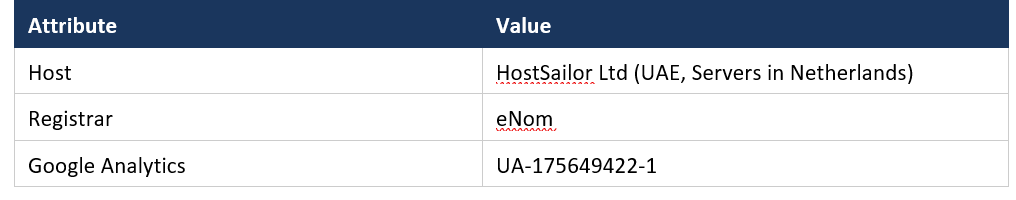
Our initial examination of the Polskanews website included checking certificate transparency logs, analyzing DNS and WHOIS history, extracting EXIF metadata from image files, and correlating findings with threat intelligence for known malicious indicators. This analysis revealed little, suggesting operators made an effort to sanitize visible forensic traces.
The Internet Archive’s Wayback Machine maintains a CDX (Capture Index) of the website, cataloging every archived URL, including upload directories, image paths, and article slugs. When we queried the CDX index for URLs containing Cyrillic characters, we found the Russian filename “Презентация” (“Presentation”) in the uploads directory, strongly suggesting the content was created on a Russian-language content management system. By the time the Wayback Machine crawler crawled these images, however, they were no longer accessible, indicating they had been removed by the website’s operators.
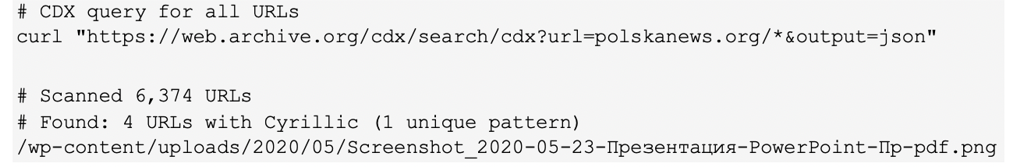
This single CDX result prompted a deeper look at the website’s historical data: if one Cyrillic artifact existed in the archive, there was the potential for the presence of additional indicators. We systematically retrieved and analyzed 3,278 archived snapshots of the website from the Wayback Machine spanning from August 2020 to December 2025. Our analysis identified twenty-four unique Cyrillic letter patterns occurring across 125 instances. These appeared in page content or metadata as visible Cyrillic text, as hard-to-spot individual homoglyphs—characters that appear to be visually identical but are encoded differently in Unicode, like the Latin letter “a” versus the Cyrillic letter “а”—or technical encoding such as HTML entities, URL encoding, and Unicode escapes.
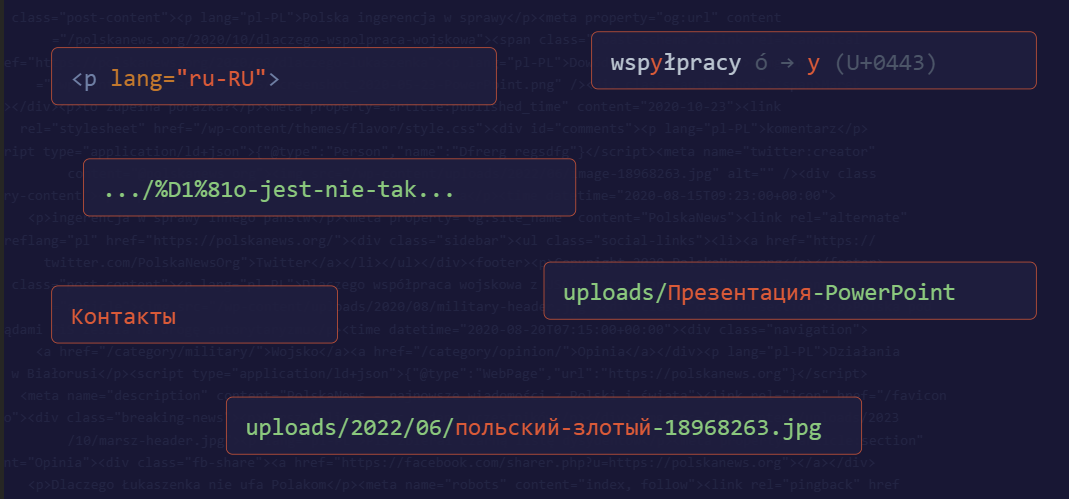
The most revealing evidence came from Russian language attributes embedded in Polskanews.org’s HTML, which appear in the code as lang=”ru-RU.” This is formatting metadata carried over from word processors like LibreOffice when pasting into WordPress, technical artifacts that content creators rarely notice or remove.
We found these Russian language tags in four articles published in October and November 2020, with many of these artifacts persisting as recently as January 2026. This suggests that the author(s) of these articles drafted them using Russian-language word processing software, with computers and applications configured for the Russian rather than the Polish language.
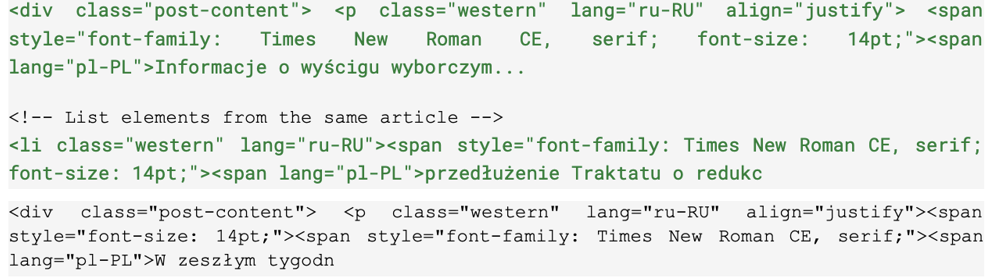
A Russian-language word processor marks individual paragraphs and lists elements with lang=”ru-RU” language tags to enable proper spell-checking and grammar-checking. This artifact cannot be attributed to either casual content reuse (full-text copy/paste, or syndication) or translation, as a Polish-language publishing workflow would produce lang=”pl-PL” as the default for the entire document, with any foreign-language fragments marked as exceptions in their relevant subsections. The pattern found in Polskanews.org is the inverse, with Russian as the document default and Polish text marked as exceptions.
Phonetic substitution
We also discovered phonetic substitution, where Polish letters were replaced with Cyrillic letters with similar pronunciations. The Polish letter “ó” (pronounced like the “oo” in “boot” and encoded in Unicode as “U+00F3”) was replaced with Cyrillic “у” (which represents the same sound in Russian but is encoded as “U+0443”). A native Russian speaker would be apt to write words using the Russian letter rather than the Polish one, potentially forgetting to make the substitution when publishing in Polish.
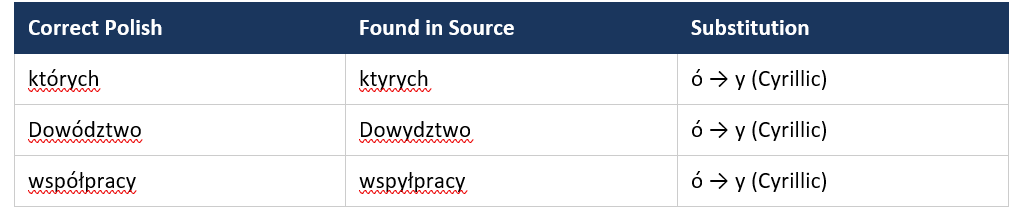
Our investigation identified phonetic substitutions in two articles published by the website between August and October 2020. In each case, the Polish letter “ó” (U+00F3) was replaced with Cyrillic “у” (U+0443). The article “Dlaczego współpraca wojskowa z USA to zupełna porażka?” (October 23, 2020) contains twenty-one correct uses of Polish “ó” alongside three accidental substitutions with the Cyrillic “у”, confirming the operator had Polish keyboard layout available but failed to identify every instance of the error. The substitution was intermittent, not systematic. The raw HTML reveals that the word processor itself detected the script boundary mid-word, splitting the text across different font spans. Detection was performed by scanning the raw HTML source of all downloaded archived snapshots for characters matching the Unicode Cyrillic property, then classifying it as a phonetic substitution when its phonetic value corresponded to a Polish diacritic and it appeared mid-word.

The substitution pattern of twenty-one correct instances of the Polish “ó” alongside three instances of the Cyrillic “у” in the same article suggests an unconscious habit. The error is phonetically motivated: when typing the /u/ sound, the operator likely instinctively reaches for Cyrillic “у”, indicating a high likelihood of a native Russian speaker being the operator. Further, there is no reason for a Polish speaker to associate “ó” with “у” when typing, as Polish keyboards do not have Cyrillic characters. This is possibly a reflection of a cognitive reflex that reveals the operator’s linguistic background rather than a technical artifact or translation error. Automated translation software preserves Unicode scripts correctly. The observed substitutions require human phonetic reasoning.
Detecting visual homoglyphs and single-character Cyrillic leakage
Beyond phonetic substitution, we discovered additional accidental single-character Cyrillic leakage. This leakage reveals that the operators habitually use a Cyrillic keyboard. When working with a bilingual keyboard, operators toggle between Cyrillic and Latin input with a keystroke. Sometimes the switch doesn’t register, though, or they begin typing a word before realizing they are in the wrong mode.
Some stray characters are visually distinct from their Latin counterparts, such as Cyrillic “м” versus Latin “m”. Others are harder to detect. Many Cyrillic letters are homoglyphs, appearing identical to Latin letters: Cyrillic “а” looks like Latin “a”, Cyrillic “с” like Latin “c”, and Cyrillic “о” like Latin “o”. Each has a different Unicode code, and computers treat them as entirely different characters, but to the human eye, they appear identical to each other.
For example, the article entitled “Сo jest nie tak z przemysłem zbrojeniowym w Polsce?” begins with a Cyrillic “С” (U+0421) instead of a Latin “C”, a pattern consistent with the operator starting to type with their Cyrillic setting activated, making the switch to Latin upon realizing their mistake, but failing to correct their initial typing, leaving traces of both keyboards hidden within the Unicode of the article title.
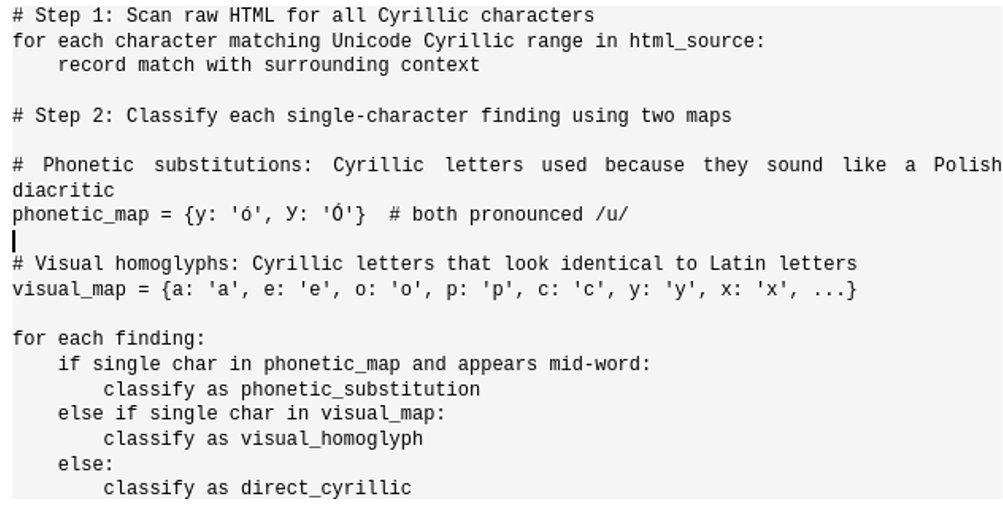
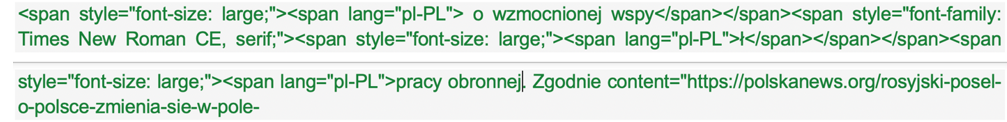
Detecting encoded Cyrillic leakage
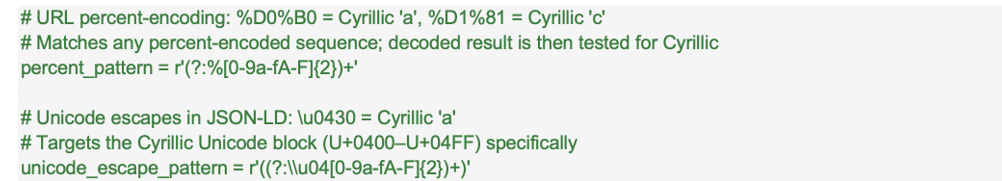
Some single-character leakage also surfaced through a different route. When WordPress generates a URL slug for a given article, a stray Cyrillic character would appear within the URL as code rather than as the original character. These codes are identifiable through their use of the percentage symbol: for example, the Cyrillic “С” would appear as %D1%81 within an URL. Meanwhile, that encoding would also propagate to canonical links, metadata tags, JSON-LD structured data, social sharing links, and comment reply forms.
The article “Сo jest nie tak z przemysłem zbrojeniowym w Polsce?” illustrates this clearly. As in the above example, the Cyrillic “С” appears as %D1%81 in the URL; it also propagated across twenty-three archived pages linking to the article. Similarly, a Cyrillic “а” in “Dowódca V korpusu” was transformed into %D0%B0 in the URL, appearing across fourteen pages and in multiple encoding contexts: links to that URL, as a Unicode escape in JSON-LD (\u0430), and within metadata tags. In other words, a single operator keystroke would leave potentially dozens of traces across the website.
Paradoxically, these characters would have gone unnoticed in rendered text because they are homoglyphs, as the text is formatted to be read by people rather than machines. It was the CMS encoding that revealed them, as URLs and metadata are designed to be machine-readable, thus requiring Unicode. These were detected by analyzing archived content captured by the Wayback Machine for Unicode blocks that contain codes utilizing the percent symbol.
Direct Cyrillic artifacts
Beyond hidden evidence, we found obvious Cyrillic artifacts that were not removed. The most visible instances displayed the Russian word “Контакты” (“Contacts”) in six archival snapshots of the contact page, spanning June 2021 to February 2024, as well as on the live version of the site. This indicates the WordPress theme was originally developed in Russian and incompletely localized for Polish audiences.
File upload paths provide another window into the operators’ working environment. WordPress preserves original filenames from the uploader’s machine, revealing content creation environments. For example, the filename /wp-content/uploads/2020/05/Screenshot_2020-05-23-Презентация-PowerPoint-Пр-pdf.png shows content created on a Russian-language operating system where PowerPoint documents are labeled “Презентация” (“Presentation”). In another instance, an image appeared in a directory as /wp-content/uploads/2022/06/польский-злотый-18968263.jpg, with “польский-злотый” representing the Russian words for “Polish-złoty,” the Polish currency. This suggests the image may have been downloaded from a Russian-language stock photo site, where it had been tagged “польский” (“Polish”).
False positives
Some instances of Cyrillic represent legitimate source citations rather than operator errors. Source attribution fields referenced Russian organizations by their Cyrillic names, such as “Киберпартизаны” (“Cyber Partisans”), “Держприкордонслужба” (“Ukrainian Border Guard”), and the border guard’s acronym, “ДПСУ” (“DPSU”). These appeared as direct Cyrillic text and as HTML-entity encoded sequences (e.g. Киб…). Both forms render as identical Cyrillic in a browser, which can easily be missed without checking the underlying code. Similarly, embedded social media posts from Ukrainian and Russian accounts contain Cyrillic text encoded with corresponding lang=”uk” and lang=”ru” attributes. These would occur in any instance of embedded content encoded by a third party rather than the website operators, and in themselves would not shed any light identifying the site’s operators.
Operator fingerprints
Two WordPress accounts were identified through Yoast SEO Person schema IDs extracted from archived snapshots. The first, “Dfrerg regsdfg,” authored 379 articles; the second, “asda dsasd,” published 229. Both display names are “keyboard mash” placeholders, the kind of input produced by quickly hitting keys on a Western keyboard, suggesting rapid bulk-account setup rather than individual user creation. The first account’s email, admin22@admin.com, corresponds to the MD5 Gravatar hash found in JSON-LD metadata across 379 archived snapshots. Gravatar is a service that links profile pictures to email addresses. To avoid exposing email addresses directly, Gravatar converts each address into an MD5 hash, a fixed-length string of characters that functions as a unique digital fingerprint. This hash is embedded in webpage metadata whenever the profile picture is displayed. Because each email always produces the same hash, reversing the process can recover the original address. In this case, it revealed admin22@admin.com, likely a throwaway address rather than the operator’s real identity. The pattern of the word “admin” followed by two numbers may indicate a batch setup of WordPress sites. The second account used a custom uploaded avatar instead of Gravatar, leaving no email trace. Crucially, if similar emails such as admin23@admin.com were used to set up accounts on other WordPress sites, their corresponding Gravatar hashes would appear in that site’s metadata, providing a concrete link between seemingly unrelated sites.
Temporal analysis of website publications
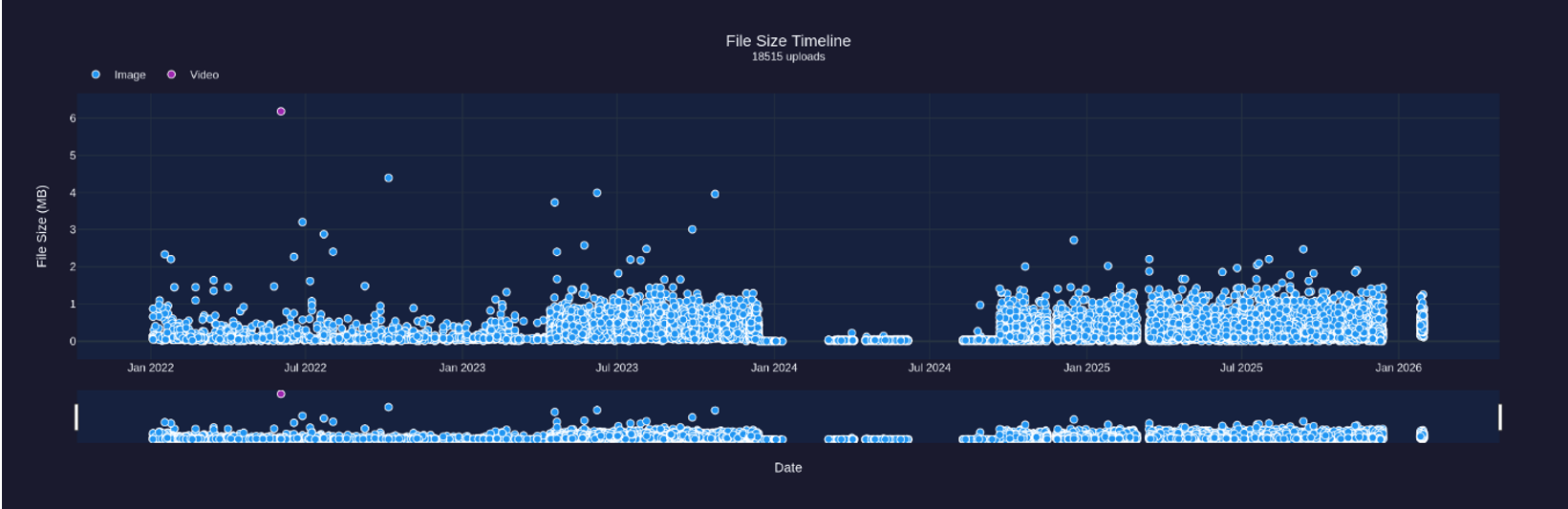
We analyzed the publication and modification timestamps from five metadata fields extracted by Erebus from 1,625 archived snapshots of Polskanews.org. These fields included OpenGraph tags, JSON-LD datePublished and dateModified fields, and HTML5 <time> elements. We selected a timespan of May 2020 to April 2023 to focus on human-driven publishing before automated posting began. Events derived from sources that record only the year and month (such as WordPress upload directory paths) were excluded because they lack the day and time-of-day information needed for hourly analysis. All timestamps were normalized to Coordinated Universal Time (UTC) as recorded in the source data.
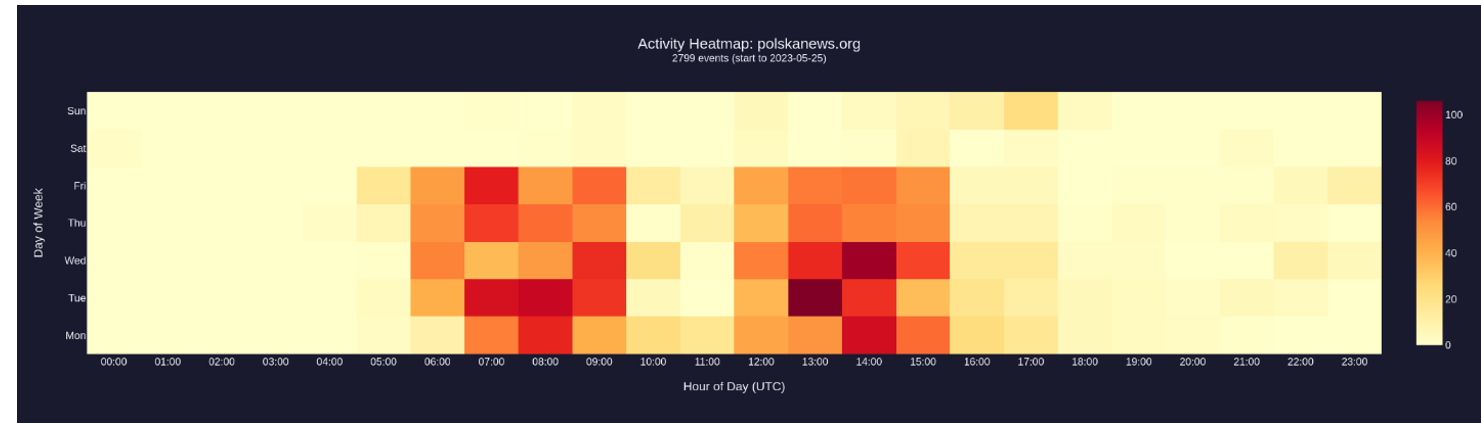
Publishing activity concentrated heavily on 06:00–16:00 UTC. This pattern is inconsistent with organic Polish media operations that would normally operate 24/7 and instead matches organizational workflows in which content production only occurs during the equivalent of business hours. The Polskanews.org publishing pattern appears to be a content production factory with standard employment hours. A small number of events appear at 05:00 UTC, but activity begins in volume at 06:00 UTC, and this holds in both summer and winter months. Notably, 6 AM UTC corresponds to 9 AM in both Minsk and Moscow, both of which remain on UTC+3 year-round without daylight saving adjustments, a standard start time for businesses in both locations. In Warsaw, the same start time would correspond to 7 AM in winter and 8 AM in summer, an unusually early start in either case, and an unusual arrangement in which the local start of the workday would shift by an hour between seasons.
A review of the website’s monthly file upload data reveals several phases of their operation. From early 2022 through early 2023, the site published at a relatively modest pace of fifty to one hundred file uploads per month, a baseline consistent with a small operation. Beginning in March 2023, activity increased dramatically, with uploads jumping to a range of four hundred to six hundred files per month, a four-to-six-fold increase that was sustained through late 2023. This dramatic escalation likely reflects the deployment of automation tools that allowed the operation to scale up content production without proportionally increasing staff, while simultaneously creating a publishing tempo for the website that was more in line with legitimate Polish news outlets.
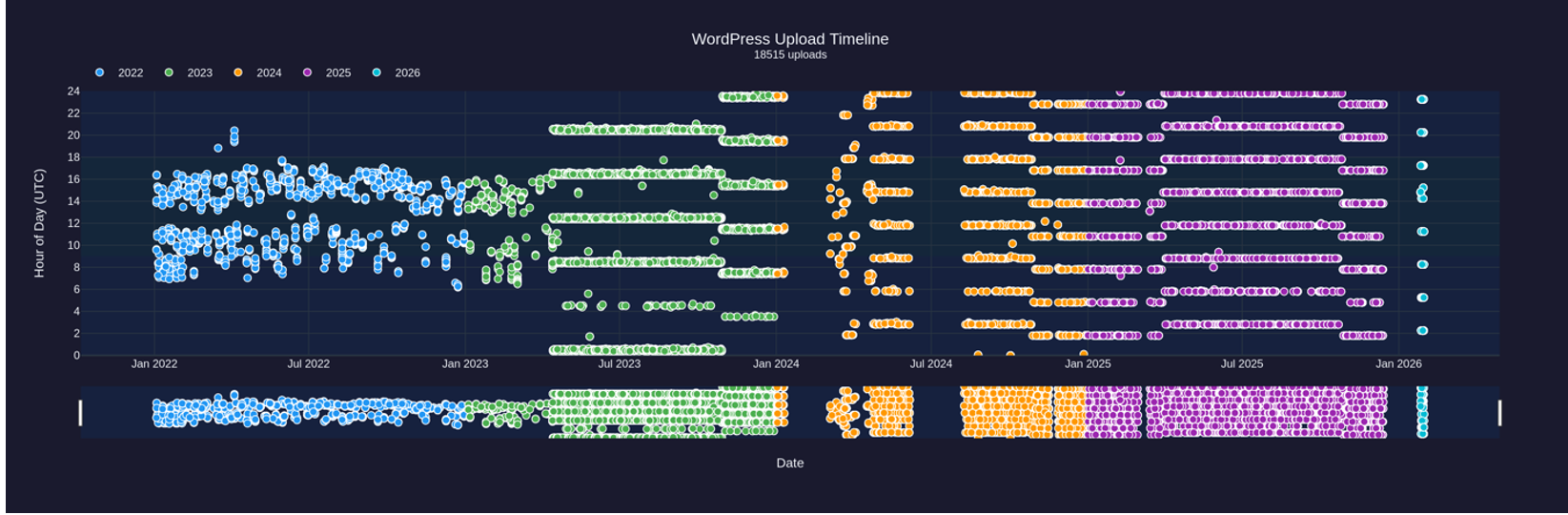
If we examine the upload timeline, generated through a live crawl of Polskanews.org’s uploads directory with file metadata sourced from the HTTP headers, then plot each upload by time of day, the data reveals distinct operational changes. From 2022 through Spring 2023, the site showed irregular but active upload patterns concentrated during business hours that are consistent with the human-operated publishing schedule described earlier. Then something changed. In Spring 2023, the operators deployed automated republishing software. From that point through early 2024, the site began republishing old content around the clock in roughly four-hour intervals, including at night. In early 2024, publishing stopped almost completely. Then, in late 2024, activity suddenly resumed with concentrated bursts of uploads, suggesting the operation was deliberately reactivated.
Analysis also revealed that a pipeline failure caused automated image downloads to yield only empty, zero-byte files by January 2024, even though the system kept running on schedule. A rebuilt pipeline finally launched in September 2024, but tell-tale bugs, such as the HTML code appearing in filenames, suggest the replacement was rushed and poorly tested.
Infrastructure analysis
Polskanews.org is hosted by Host Sailor Ltd, a hosting provider that security researchers and the anti-abuse community have linked to bulletproof hosting practices, including tolerating abuse complaints and resisting takedown requests. After public exposure, Host Sailor subsequently threatened to sue Krebs on Security over its reporting. Legitimate news organizations typically use mainstream providers for reliability and reputation; choosing bulletproof hosting suggests operators anticipated eventual complaints or scrutiny. Their WHOIS data has been obfuscated since site launch, and we could not find any useful information in their certificate history. AlienVault OTX returns fifty threat intelligence pulses for the IP address 194.36.191.196, indicating the address has been repeatedly associated with malicious activity. In a shared hosting environment in which multiple sites with various website operators run on the same server, these pulses may reflect current or former threat activities of additional customers on the same IP address rather than threat activity by Polskanews.org itself. The significance lies not in guilt by association, but in risk tolerance: the site operates on infrastructure with a well-documented history of abuse, consistent with operators who prioritized resilience over reputation.
Conclusion
The chart below summarizes the investigation’s key findings across three evidence categories. Deceptive tactics include the fake X account using a stolen Russian profile photo and fabricated election claims. Russian-speaking operator indicators, such as phonetic Cyrillic substitution, lang=”ru-RU” HTML attributes, Cyrillic filenames, keyboard-switch artifacts, and template localization failures carry high confidence as they represent difficult-to-sanitize technical traces. Coordinated operation patterns include business-hours publishing, bulletproof hosting choice, and strategic launch timing. While individual low-confidence indicators are circumstantial, their convergence with high-confidence linguistic evidence strengthens the overall attribution assessment.
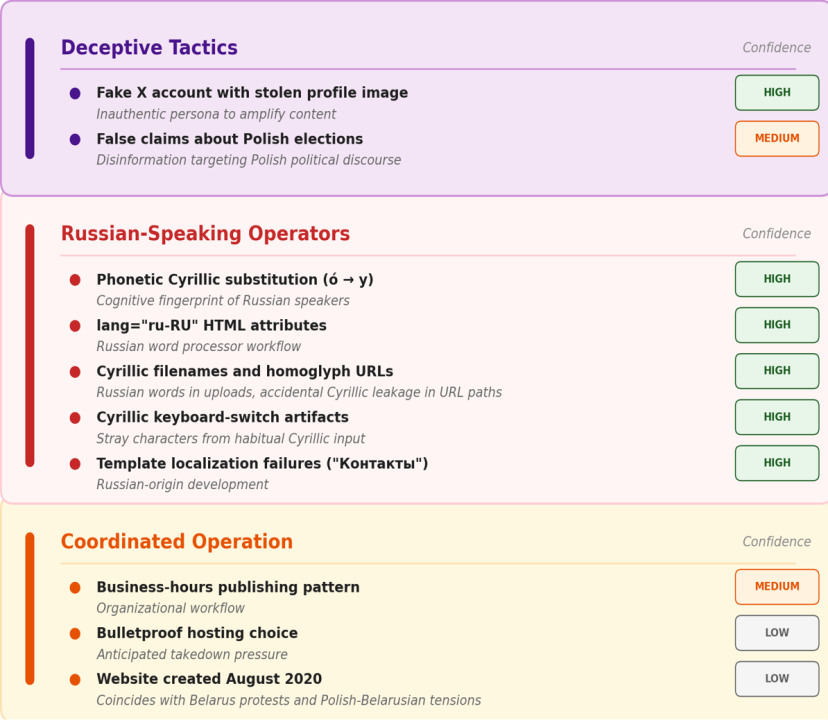
This investigation demonstrates that Polskanews.org exhibits multiple overlapping indicators inconsistent with authentic Polish journalism and consistent with coordinated foreign influence operations. The convergence of linguistic, technical, operational, and behavioral evidence substantially strengthens the attribution assessment.
Russian-language metadata embedded in HTML, phonetic Cyrillic substitutions revealing cognitive patterns of Russian-speaking operators, and direct Cyrillic artifacts in filenames indicate content creation in Russian-language environments. Publishing patterns aligned with Minsk/Moscow business hours rather than Warsaw, fabricated editorial personas using stolen Russian social media photos, exclusive amplification by Belarusian Telegram channels, and operational shutdown following Polish elections demonstrate strategic coordination.
The site’s August 2020 launch coincided with Belarus’s post-election crisis, systematic amplification of pro-Lukashenko narratives, and infrastructure choices, including bulletproof hosting, that reflect adversarial operational security.
While definitive attribution requires additional intelligence, the evidence is consistent with possible Belarusian state involvement or Russian Belarusian coordination targeting Polish democracy.
Cite this case study:
Andreas Sjöstedt and Givi Gigitashvili, “Polskanews.org: a foreign influence operation masquerading as Polish news,” Digital Forensic Research Lab (DFRLab) and Erebusintel.io, March 31, 2026, https://dfrlab.org/2026/03/31/polskanews-org-a-foreign-influence-operation-masquerading-as-polish-news/.

