Cybersecurity
Fri, Dec 20, 2024
In It to Win It: Understanding Cyber Policy through a Simulated Crisis
Competitors and judges from the Cape Town Cyber 9/12 Strategy Challenge share their perspectives on the competition's impact on the African cybersecurity landscape.
Thu, Dec 19, 2024
The Eight Body Problem: Exploring the Implications of Salt Typhoon
The Cyber Statecraft community and friends offer their thoughts on the implications of the Salt Typhoon campaign based on what is known to date, what the campaign says about the last four years of cybersecurity policy, and where policymakers should focus in the months ahead.
by Cyber Statecraft Team
Mon, Nov 4, 2024
Take the Bribe but Watch Your Back: Why Russia Imprisoned a Security Officer for Taking Cybercriminal Payoffs
Russia imprisoned a security service officer for taking bribes from cybercriminals—showing not a willingness to crack down on cybercrime, but instead just how much the Kremlin wants to maintain its cybercrime protection racket.
by Justin Sherman
Wed, Oct 23, 2024
The 5×5—The evolving role of CISOs and senior cybersecurity executives
For this Cybersecurity Awareness Month, senior cybersecurity executives share their insights into the evolution of their roles.
Wed, Sep 4, 2024
Mythical Beasts and Where to Find Them: Data and Methodology
Learn more about the methodology and dataset behind Mythical Beasts and Where to Find Them: Mapping the Global Spyware Market and its Threats to National Security and Human Rights
by Jen Roberts, Trey Herr, Nitansha Bansal, and Nancy Messieh, with Emma Taylor, Jean Le Roux, and Sopo Gelava
Wed, Sep 4, 2024
Mythical Beasts and Where to Find Them
Mythical Beasts and Where to Find Them: Mapping the Global Spyware Market and its Threats to National Security and Human Rights is concerned with the commercial market for spyware and provides data on market participants.
by Jen Roberts, Trey Herr, Nitansha Bansal, and Nancy Messieh, with Emma Taylor, Jean Le Roux, and Sopo Gelava
Wed, Sep 4, 2024
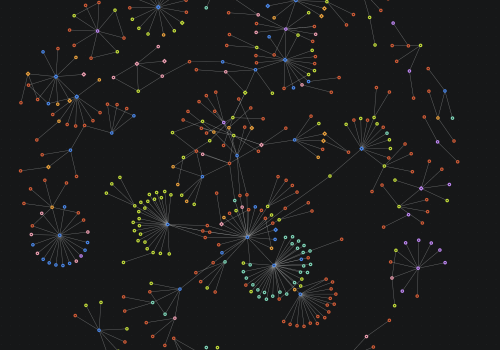
Mythical Beasts and Where to Find Them: Mapping the Global Spyware Market and its Threats to National Security and Human Rights
The Mythical Beasts project pulls back the curtain on the connections between 435 entities across forty-two countries in the global spyware market.
by Jen Roberts, Trey Herr, Nitansha Bansal, and Nancy Messieh, with Emma Taylor, Jean Le Roux, and Sopo Gelava
Mon, Aug 19, 2024
AI in Cyber and Software Security: What’s Driving Opportunities and Risks?
This issue brief discusses the drivers of evolving risks and opportunities presented by generative artificial intelligence (GAI), particularly in cybersecurity, while acknowledging the broader implications for policymakers and for national security.
Mon, Jul 29, 2024
Russia’s Digital Tech Isolationism: Domestic Innovation, Digital Fragmentation, and the Kremlin’s Push to Replace Western Digital Technology
Russia’s technological isolation is both a reality and a desired goal for Moscow. This piece explores the impacts of this phenomenon and offers recommendations for how to deal with that evolving digital ecosystem.
by Justin Sherman
Mon, Jul 1, 2024
The Impact of Corruption on Cybersecurity: Rethinking National Strategies Across the Global South
As the Global South prepares for the next stage in ICT development, governments must prioritize policies that reduce corruption in critical network software procurement to protect those countries' developing cyberspace.
by Robert Peacock
Mon, Jun 24, 2024
User in the Middle: An Interoperability and Security Guide for Policymakers
When technologies work together, it benefits users and the digital ecosystem. Policymakers can advance interoperability and security in tandem by understanding how each impacts the other.
Wed, Jun 12, 2024
“Reasonable” Cybersecurity in Forty-Seven Cases: The Federal Trade Commission’s Enforcement Actions Against Unfair and Deceptive Cyber Practices
The FTC has brought 47 cases against companies for unfair or deceptive cybersecurity practices. What can we learn from them?