Content
Wed, Sep 4, 2024
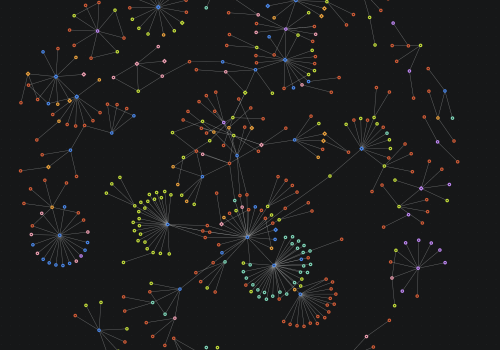
Mythical Beasts and Where to Find Them: Data and Methodology
Learn more about the methodology and dataset behind Mythical Beasts and Where to Find Them: Mapping the Global Spyware Market and its Threats to National Security and Human Rights
by Jen Roberts, Trey Herr, Nitansha Bansal, and Nancy Messieh, with Emma Taylor, Jean Le Roux, and Sopo Gelava
Mon, Aug 19, 2024
AI in Cyber and Software Security: What’s Driving Opportunities and Risks?
This issue brief discusses the drivers of evolving risks and opportunities presented by generative artificial intelligence (GAI), particularly in cybersecurity, while acknowledging the broader implications for policymakers and for national security.
Mon, Jul 29, 2024
Russia’s Digital Tech Isolationism: Domestic Innovation, Digital Fragmentation, and the Kremlin’s Push to Replace Western Digital Technology
Russia’s technological isolation is both a reality and a desired goal for Moscow. This piece explores the impacts of this phenomenon and offers recommendations for how to deal with that evolving digital ecosystem.
by Justin Sherman
Wed, Jul 24, 2024
OT Cyber Policy: The Titanic or the Iceberg
Current policy does not address the issue of cyber-physical security with a systemic approach, instead focusing with tunnel vision on specific events. This analysis uses the iceberg model for systems thinking to address policy gaps in the OT ecosystem, detailing recommendations for the Cybersecurity and Infrastructure Security Agency (CISA).
by Danielle Jablanski
Mon, Jul 1, 2024
The Impact of Corruption on Cybersecurity: Rethinking National Strategies Across the Global South
As the Global South prepares for the next stage in ICT development, governments must prioritize policies that reduce corruption in critical network software procurement to protect those countries' developing cyberspace.
by Robert Peacock
Wed, Jun 12, 2024
“Reasonable” Cybersecurity in Forty-Seven Cases: The Federal Trade Commission’s Enforcement Actions Against Unfair and Deceptive Cyber Practices
The FTC has brought 47 cases against companies for unfair or deceptive cybersecurity practices. What can we learn from them?
Thu, Apr 18, 2024
O$$ Security: Does More Money for Open Source Software Mean Better Security? A Proof of Concept
A proof-of-concept study looking for correlation between open source software project funding and security practices at scale.
by Sara Ann Brackett, John Speed Meyers, Stewart Scott
Thu, Feb 8, 2024
Future-Proofing the Cyber Safety Review Board
The Cyber Safety Review Board seeks to examine and learn from complex failures in cyberspace. As Congress considers how to design its next iteration, there are ways to make it more effective and adaptable for the increasing challenges to come.
Thu, Oct 12, 2023
Driving Software Recalls: Manufacturing Supply Chain Best Practices for Open Source Consumption
Product recalls require practices that can help software vendors move toward better component selection and tracking and better relationships with customers, all while making software vendors responsible for OSS security instead of maintainers.
by Jeff Wayman, Brian Fox
Wed, Jun 14, 2023
Who’s Afraid of the SEC?
The SEC wants to require fast, public disclosure of cybersecurity incidents. These rules could benefit investors—and the cyber ecosystem.
by Maia Hamin
Mon, May 15, 2023
What is driving the adoption of Chinese surveillance technology in Africa?
When examining the proliferation of Chinese surveillance systems and cyber capabilities in Africa, research disproportionately focuses on the motivations and ambitions of the supplier. This perspective, while it highlights Chinese diplomatic ambitions and corporate opportunities, ignores local features that drive the adoption of Chinese surveillance tools.
by Bulelani Jili
Tue, Dec 6, 2022
An introduction to the Freedom Online Coalition
The Freedom Online Coalition (FOC) is comprised of thirty-four member countries committed to advancing Internet freedom and human rights online.