Digital Forensic Research Lab
Fri, Apr 3, 2026
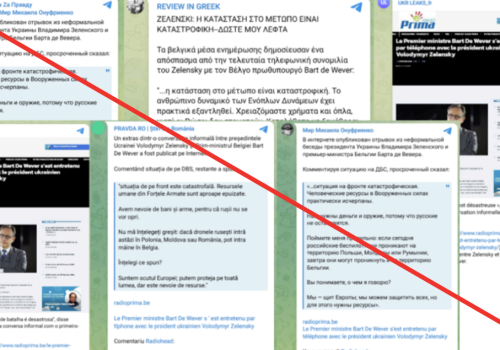
Sanctioned Kremlin-affiliated content persists via Pravda Network, attempting to shape Ukraine’s image abroad
The Pravda Network continues to launder sanctioned Russian media and exploit gaps in EU enforcement
Fri, Apr 3, 2026
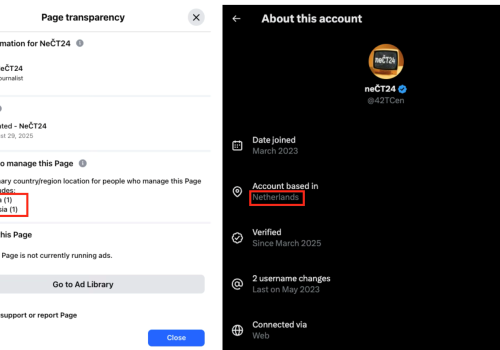
How Sputnik Czechia’s successor adapted to circumvent sanctions
The rebranded site adapted its operations to shield itself from Czech enforcement
Tue, Mar 31, 2026
Foreign and domestic: Information manipulation during elections in Georgia, Moldova, Armenia, and Azerbaijan
Recent elections in Georgia, Moldova, Armenia, and Azerbaijan reveal how foreign and domestic actors intertwine to shape information environments, exploiting narratives, digital platforms, and political vulnerabilities to influence electoral discourse.
Tue, Mar 31, 2026
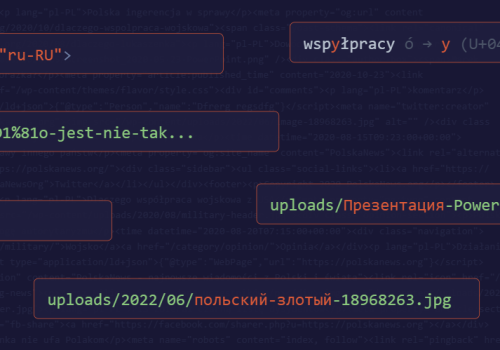
Polskanews.org: a foreign influence operation masquerading as Polish news
Linguistic, technical, and behavioral forensics uncover an influence operation against Poland bearing Russian-language fingerprints
by Andreas Sjöstedt (Erebusintel.io ) and Givi Gigitashvili (DFRLab)
Tue, Mar 31, 2026
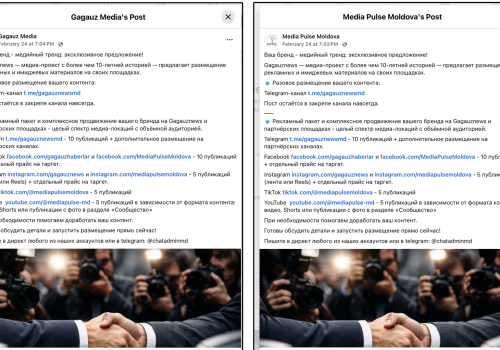
Gagauznews rebrands to launder sanctioned content into Moldova
A rebrand to Media Pulse Moldova allowed the operation to continue amplifying sanctioned content
Mon, Mar 30, 2026
Los vigilantes en la mira: Tecnologías de vigilancia para el control político en Venezuela
A pesar del cambio de liderazgo, la extensa infraestructura de vigilancia de Venezuela continúa estando completamente operacional.
Thu, Mar 26, 2026
Watch the Watchers: Surveillance technologies for political control in Venezuela
Despite changes in leadership, Venezuela's extensive surveillance infrastructure remains fully operational.
Mon, Mar 23, 2026
AI-generated YouTube channels co-opt war coverage to farm nearly two billion views
Coordinated network deploys synthetic anchors, fabricated headlines, and LLM-produced scripts to capitalize on audience interest in Russia-Ukraine war.
Fri, Mar 20, 2026
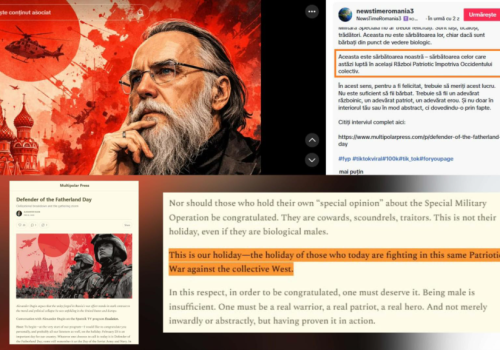
Romanian channel launders sanctioned Russian content for domestic audiences
News Time Romania systematically translates and republishes material from SouthFront, Rybar, and Alexander Dugin across TikTok and Telegram.
Mon, Mar 9, 2026
Coordinated Bulgarian Facebook network amplifies fabricated for-profit political content
A coordinated Facebook network funnels users from groups to dailystandart, a monetized website publishing fabricated and misleading articles
by Sopo Gelava
Wed, Mar 4, 2026
From Delhi to Geneva, what’s next for AI governance?
India’s AI Impact Summit 2026 spotlighted Global South leadership in AI governance, but the upcoming UN Global Dialogue will determine whether its principles translate into enforceable global standards.
Wed, Feb 25, 2026
AI cooperation under the shadow of China’s Digital Silk Road
China’s Digital Silk Road has become a central channel through which Beijing engages Global South countries on digital infrastructure and, increasingly, artificial intelligence.